- • The public often perceives digital identity as just the user interface (portals, apps), overlooking the critical underlying infrastructure
- • Digital identity forms a core component of Digital Public Infrastructure, alongside payments and data exchange, answering the question of “who”
- • Digital identity, digital credentials, and digital wallets are distinct concepts
Above: Artwork making use of an illustration by RoseStudios/DepositPhotos.
Proof of Life
This is the third article about Digital Public Infrastructure published by Nicole Greene on her Substack. The first article is here. Thew second article is here. Proof of Life is published with her permission.
Every functioning society runs, quietly and constantly, on recognition.
Recognition that a child was born. Recognition that a person is who they say they are. Recognition that a business is registered; a doctor is licensed; a widow is entitled to a benefit; a traveller may cross a border. Recognition that a payment should reach this person and not that one.
Before a state can serve anyone well, it has to be able to recognise them reliably.
That is why digital identity matters.
It is also why people tend to misunderstand it.
To much of the public, modernisation looks like the surface of things: the portal, the app, the online form and faster lines. What they do not always see is the institutional architecture underneath, without which the surface remains cosmetic. The state can launch all the portals it likes, but if the underlying systems cannot establish who a person is, who is authorised to act, and who is entitled to receive what, the front end is just better packaging on the same old confusion.
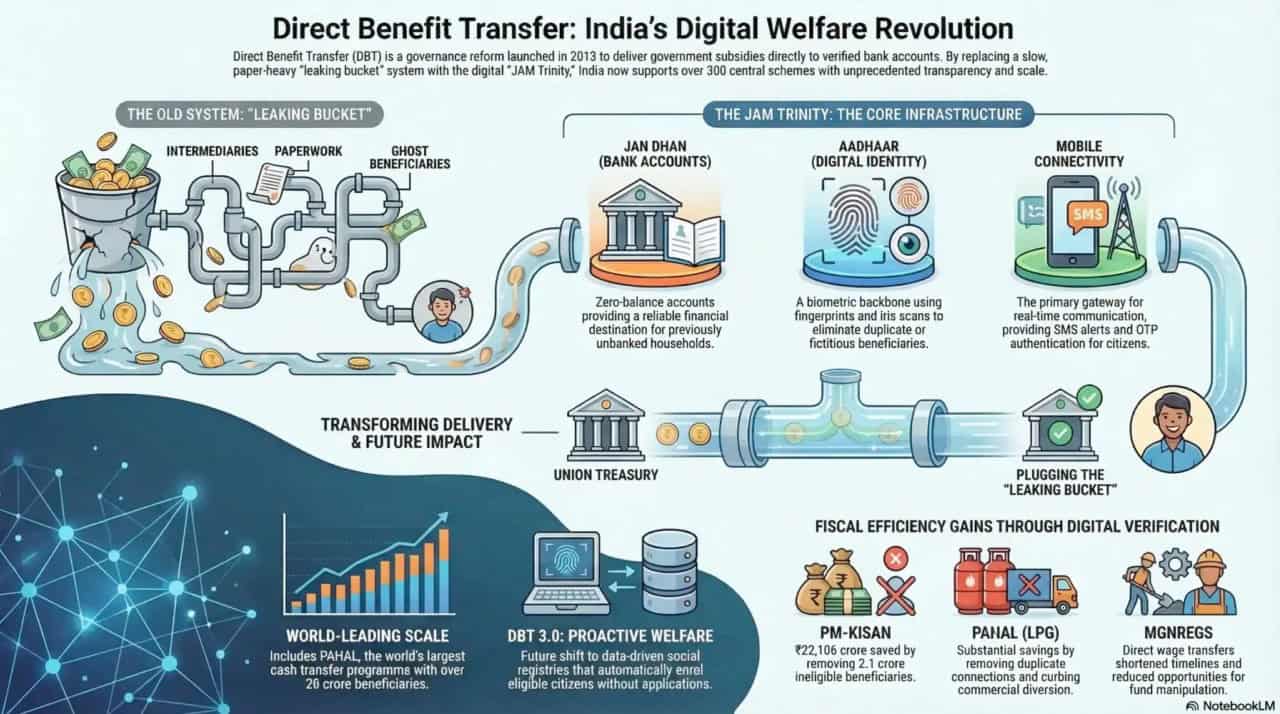
Digital identity is part of that deeper architecture. It is one of the foundational layers of Digital Public Infrastructure (DPI), alongside payments and data exchange. Payments move value. Data exchange moves information. Identity answers the prior question: who, exactly, is the system dealing with?
When you open a bank account, or sit an exam, some institution must answer a basic question before anything else can happen: are you, in fact, the right person?
For those of us who already have documents, cards, numbers, and accounts, that question can seem like a nuisance: another form, another photocopy, another request to upload the same passport and proof of address to yet another portal that claims to be making life simpler.
For businesses, it appears as cost: repeated onboarding, compliance checks, KYC procedures, fraud controls, document reviews, verification delays.
For hundreds of millions of people around the world, however, it appears as something more disturbing. It appears as exclusion.
The World Bank’s ID4D programme estimates that roughly 800 million people worldwide still lack official proof of identity, while another 2.8 billion lack access to a government-recognised digital identity for online transactions. Over half of those without official ID are children whose births were never registered. In low-income countries, women remain less likely than men to have identification. To be undocumented in this sense is not simply to be inconvenienced. It is to be partially invisible to the systems that distribute rights, services, money, and legal recognition.
You cannot build a functioning digital state if the state cannot reliably recognise people.
That is why digital identity has become such a significant global policy priority. It is not because governments have suddenly developed a taste for more databases. It is because every serious effort to digitise public services eventually crashes into the same obstacle: you cannot build a functioning digital state if the state cannot reliably recognise people.

Chairman of the National Identification Registration Authority (NIRA) bishop Conrad Pitkin handed over a national identification card to prime minister Dr. Andrew Holness, at the official launch of the NIRA at the Central Sorting Office in Kingston.
What digital identity is… and what it is not
In ordinary life, identity means the rich, deeply human business of who we are: family, culture, memory, language, faith, history, belonging.
Digital identity means something narrower and more administrative than the word suggests in our everyday speech.
It means a machine-verifiable way of proving that you are the person you claim to be, to a system that does not know you.
That proof usually rests on some combination of a unique identifier, biographical information, and an authentication mechanism – perhaps a PIN or a one-time code, or, in some systems, biometrics such as fingerprints or facial recognition. The mix differs by country and by design, but the purpose is the same. The system must be able to distinguish one person from another in a way it considers reliable enough to act on.
This is what policy people mean by foundational digital identity. Foundational because it sits beneath everything else. It is not a feature added late in the process, it is one of the conditions that makes the rest possible.
The part that gets confusing
Three terms get thrown around as if they were interchangeable: digital identity, digital credentials, and digital wallets. They are not the same thing.
Your foundational digital identity centres on the fact that you exist in a recognised system.
A credential is a verified claim about you. It might prove that you hold a medical licence, earned a degree, own a company, or have the right to receive a service.
The wallet is the tool that can store and present those credentials. It usually takes the form of a secure application on a phone or device.
Identity is the root. Credentials are the proofs. The wallet is the container.
This distinction matters because the future of identity is not simply about replacing plastic cards with digital ones. It is about making proof more precise and less wasteful.
At present, people routinely hand over far more information than a transaction actually requires. You show a driver’s licence to prove your age and reveal your full name, home address, and exact date of birth in the process. You submit an entire bundle of documents to prove one narrow fact. It is a blunt, over-sharing way of establishing trust.
Digital credentials and wallets are attractive because they offer a more selective model. Instead of presenting your whole identity file, you present only the relevant proof. Not here is everything about me. Instead, here is the fact you need to know.
That shift is significant.
How Estonia’s e-ID works
The European Union is already advancing this logic through its Digital Identity Wallet under eIDAS 2.0. By the end of 2026, each EU Member State is expected to offer at least one wallet to citizens, residents, and businesses, with broad acceptance by regulated sectors to follow. The architecture matters as much as the app: data is designed to live on the user’s device rather than in one all-seeing central repository, and non-digital alternatives for essential services are explicitly protected.
That last point is not incidental. It is one of the clearest signs that the global conversation has matured from “how do we build this?” to “how do we build this without creating a new class of exclusion?”
Why this matters to the average citizen
For citizens, the practical benefits are not difficult to imagine, because they are essentially the reverse image of everyday friction.
A better identity layer means less repetitive proof. Fewer photocopies. Fewer requests to reintroduce yourself to systems that ought to be capable of learning who you are once and remembering it responsibly. It means less carrying of the cargo.
That matters in routine moments: opening a bank account, verifying a licence, updating a record, signing a contract, proving eligibility. It matters even more in moments of disruption. A person displaced by fire, flood, hurricane, or conflict may lose paper documents precisely when official recognition becomes most urgent. A resilient digital identity layer can help ensure that assistance, benefits, and essential services do not vanish with the folder in the drawer.
It also matters because today’s alternatives are often deeply inefficient. We have built societies in which the same person proves the same thing to multiple institutions in slightly different formats, over and over again, and then wonder why public service feels slow and costly.
Digital identity, properly designed, is an attempt to reduce that waste.
Why this matters to business
The business case is perhaps less poetic, but no less important.
For firms, trust is expensive. Banks, insurers, payments platforms, and others spend enormous amounts of time and money trying to answer basic questions about customers and counterparties. Are they real? Are they who they say they are? Are they authorised? Are they compliant? Have we checked enough? Do we need to check again?
This is one reason onboarding is often so clumsy. Institutions do not just want proof. They need reusable confidence.
A strong identity layer, especially when paired with verifiable credentials, can reduce duplication, shorten onboarding, cut fraud exposure, and lower compliance costs. The World Bank estimates that reusable verifiable credentials can reduce some onboarding costs by 30 to 50 per cent. McKinsey has estimated that full digital identity implementation could unlock between 3 and 13 per cent of GDP by 2030, depending on the country. Behind those large numbers is a simpler point. Economies run more smoothly when trust is easier to establish and less wasteful to repeat.
For countries interested in improving ease of doing business, this matters enormously. Not because digital identity is some miraculous cure-all, but because it removes a common bottleneck. A business can only move as smoothly as the underlying trust architecture allows.
Why the resistance?
If digital identity offers such obvious efficiencies, why does it provoke so much unease?
Because at its core, digital identity is not mainly a technology problem. It is a trust problem expressed through technology.
The same technical design can be welcomed in one context can be feared in another. Public resistance, therefore, cannot simply be dismissed as ignorance.
Implementing digital identity solutions is a much greater challenge, politically and emotionally, than payments or interoperability. Identity touches the body. It touches law. It touches memory. It touches the long and uneven history of how states have counted people, sorted them, and acted on that knowledge.
Some fears are entirely practical. If a password is stolen, it can be changed. If a credit card is compromised, it can be replaced. If biometric data is breached, the problem is of another order. A fingerprint does not expire. A face is not easily reissued. This is one reason the data-breach concern is so powerful and so rational. People understand instinctively that some losses are more permanent than others.
Some fears are historical. In many parts of the world, systems of identification have not always arrived as instruments of convenience or inclusion. They have sometimes been tools of control. Public anxiety does not emerge in a vacuum. It often arrives with memory attached.
Some concerns are cultural or religious and deserve more seriousness than technologists sometimes grant them. In parts of the Caribbean, as in many other societies, resistance to biometric systems can be tied to questions of bodily autonomy, spiritual meaning, and apocalyptic fear. A wise government understands that legitimacy is not won by humiliating people’s beliefs, but by building systems carefully enough that the public can see where the limits are, what the safeguards are, and what remains voluntary.
The challenge of proving a person is real is becoming more urgent at precisely the moment it is becoming more fragile.
Then there is the newest fear, and perhaps the fastest-growing one: AI. In a world of deepfakes, cloned voices, synthetic identities, and increasingly cheap impersonation, the challenge of proving a person is real is becoming more urgent at precisely the moment it is becoming more fragile.
Credentials and wallets may become more valuable not in spite of this era, but because of it. A deepfake may imitate a face. It cannot so easily fake a trusted cryptographic signature. That does not solve the problem outright, but it does empower the defence.
What the world has already learned
It is impossible to discuss digital identity, in a serious way, without mentioning India’s Aadhaar system.
Launched in 2009, Aadhaar is the world’s largest biometric identity system, with roughly 1.4 billion registrations. It became the foundational layer beneath a wider stack of services and transactions, helping to expand access to bank accounts and enabling direct benefit transfers and digital payments at astonishing scale. It is the reference case for what identity can make possible when deployed broadly enough to reshape how the state and the economy interact.
Estonia offers a different model. Its e-ID system is often treated as the gold standard for rights-first digital identity: smaller in scale, built into a broader digital state, and notably more restrained in its architecture. Estonia avoided a giant central biometric vault and instead embedded identity into a wider ecosystem of distributed data, legal rules, and interoperable public services. But Estonia’s success sits within conditions many countries do not share: a small population, high digital literacy, strong connectivity, and a specific political history that made data minimisation especially resonant. Its principles travel better than its context.
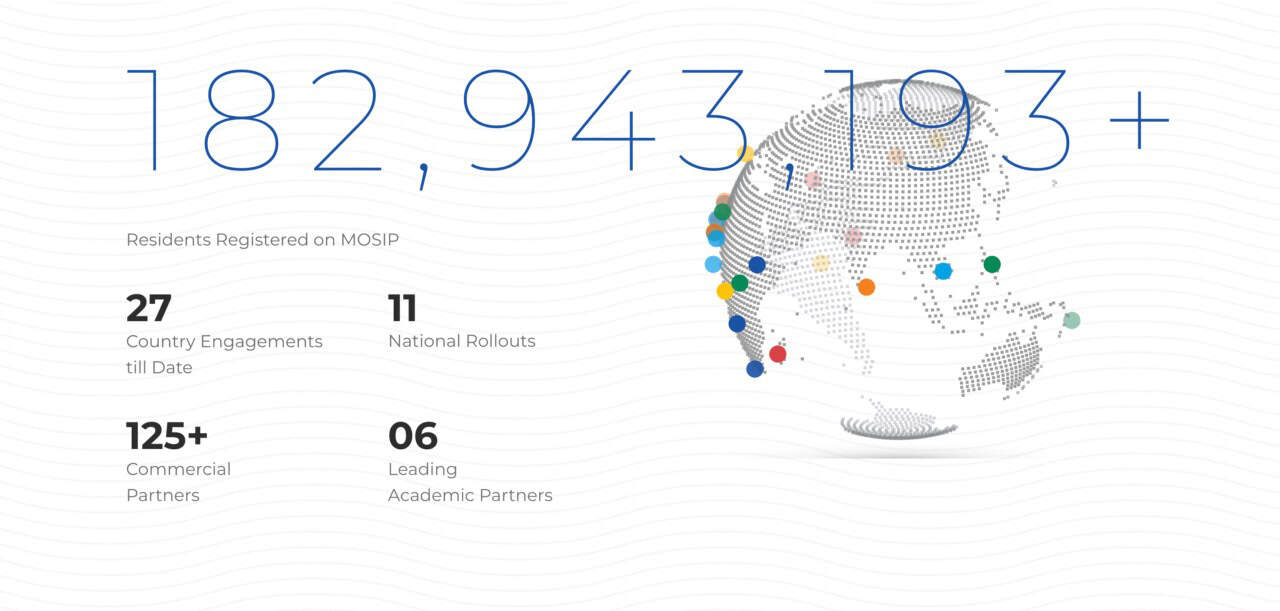
Then there is MOSIP, which may be the most consequential story in the space that ordinary readers have never heard of. The Modular Open Source Identity Platform (MOSIP) was created to address a practical problem: many countries wanted digital identity, but not the cost, inflexibility, or dependency that often came with proprietary systems.
MOSIP provides an open-source, modular alternative now deployed or piloted across multiple countries, including the Philippines, Morocco, and Ethiopia. That matters because it turns digital identity from something countries must buy as a tightly locked box into something they can adapt, own, and shape more sovereignly.
The global movement is now unmistakable. South Korea has launched a wallet trial. Australia is building a unified model. The United Kingdom has given statutory weight to its Digital Identity Trust Framework. The EU is moving toward broad wallet-based acceptance. Trinidad and Tobago has launched its wallet, VerifyTT, focusing initially on academic credentials, with plans to expand rapidly to support other verifiable credentials.
The question is no longer whether digital identity will remain a niche topic. It has already crossed that threshold. The question now is what form it will take, and under whose rules.
The Caribbean lesson
The Caribbean region has not been watching this conversation from the sidelines. It is already a part of it.
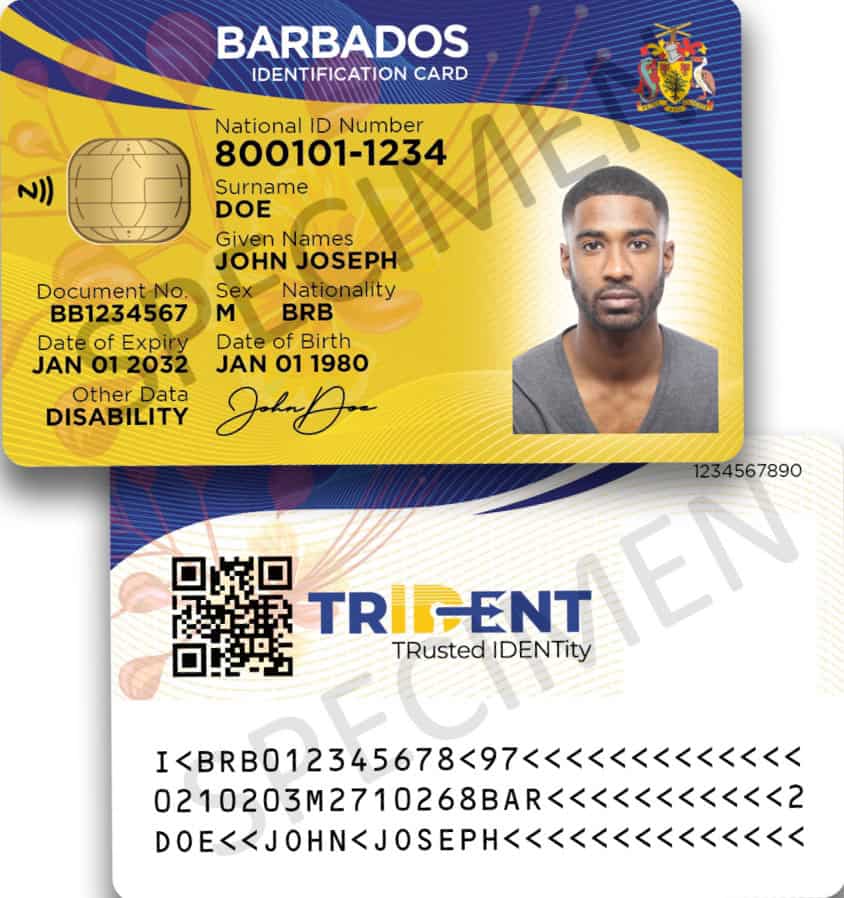
Jamaica remains the region’s most instructive case. Its original National Identification System moved too quickly past the trust question, combining mandatory biometric enrolment with penalties that made the system feel coercive. In 2019, the Supreme Court struck it down. Chief Justice Bryan Sykes’ reasoning remains an important Caribbean contribution to the global identity debate: biometric information belongs to the individual by virtue of dignity and autonomy, and the burden lies on the state to justify intrusion, not on the citizen to prove harm.
Jamaica later redesigned the system, made enrolment voluntary, strengthened safeguards, and began issuing electronic ID cards. The lesson was not that digital identity was impossible. The lesson was that legitimacy cannot be retrofitted after rollout. Trust must be built into the architecture from the beginning.
Legitimacy cannot be retrofitted after rollout.
Elsewhere in the region, progress is uneven but real. Guyana has moved quickly with digital identity and data protection legislation. Barbados has advanced its Trident ID while also encountering public resistance. Multiple Caribbean territories signed a 2023 cross-border digital ID agreement aimed at making credentials more interoperable across the region, though that vision remains at the policy-commitment stage rather than the fully operational one.
For small island states, the challenge is not only political. It is economic and institutional. The per-capita cost of building and maintaining national identity infrastructure is much higher in small states than in large ones, because the fixed costs of systems, security, and expertise do not shrink in proportion to population. MOSIP’s lower-cost, modular model therefore matters for the Caribbean in a very practical way. But even there, technology is not the whole answer. Institutional continuity, legal clarity, implementation capacity, and public confidence remain decisive.
What this really asks of government (and of the public)
The mature conversation about digital identity is not a simple contest between enthusiasm and fear.
It is about standards. Governance. Restraint. Purpose.
Whether non-digital alternatives remain available. Whether data-sharing is proportionate. Whether systems are secure enough to deserve trust. Whether identity expands access or quietly narrows it. Whether a state uses technology to spare citizens unnecessary friction, or simply relocates that friction into more sophisticated machinery.
That is why citizens need to understand the basics of the architecture beneath the app. In an environment of low trust, we tend to reflexively oppose every proposal, when we should be asking better questions.
A public that understands those questions is more likely to likely to detect the difference between serious modernisation and cosmetic digitisation, and therefore more welcome reform when the state has earned confidence.
Ultimately digital identity is not about turning people into numbers, or reducing citizenship to a card, or replacing all old systems with a futuristic wallet on a phone.
It is about modern states learning to recognise people well enough to serve them well, while asking for no more than they truly need.
That is a difficult balance, but a worthy one.
About the author
Nicole Greene is a strategic communications professional and GovTech specialist based in Trinidad and Tobago. Her work focuses on Digital Public Infrastructure (DPI) – the foundational digital systems that allow modern states to recognise, transact with, and serve their citizens – and the communications conditions that determine whether those systems are adopted, trusted, and used.
She is the founder of Women in GovTech Caribbean and the author of ADAPT (Adoption-Driven Adaptive Planning for Transformation), a communications-readiness framework for DPI implementations. Her four-part DPI series examines the architecture beneath digital government. She writes from Port of Spain, and her work can be found at nicolegreenett.substack.com.
This is the third article in a four-part series on Digital Public Infrastructure. The first, “The Invisible Architecture,” introduced DPI and the global movement behind it. The second introduced the pillar of interoperability and secure data exchange. The final article in the series will examine digital payments.