- • UTT experienced a temporary LMS outage and deferred academic activities as a precautionary measure following the breach.
- • Matt Pittinsky's return could position Blackboard as a strong alternative to Canvas
- • Instructure prioritized PR over the security and trust of its customers, failing to address the impact of the breach
Above: Illustration by wafi99d/DepositPhotos
BitDepth 1563 for May 18, 2026
On April 29, according to a statement on the website of Instructure, the creators and hosts of the Canvas Learning Management System (LMS), the company became aware of a cybersecurity incident.
Instructure made an initial statement about it on May 02.
“Instructure recently experienced a cybersecurity incident perpetrated by a criminal threat actor,” Steve Proud, Chief Information Security Officer wrote.
“We are actively investigating this incident with the help of outside forensics experts.”
On May 06, Proud updated his notification: “While our investigation continues alongside our outside forensics experts, at this stage we believe the incident has been contained.”
“Here are the steps we have taken since we became aware of the incident. We have:
– Revoked privileged credentials and access tokens associated with affected systems
– Deployed patches to enhance system security
– Out of an abundance of caution, we rotated certain keys, even though there is no evidence they were misused
Implemented increased monitoring across all platforms.”
On May 06, Proud issued what was described as the company’s “final statement” on the matter.
“Canvas is fully operational, and we are not seeing any ongoing unauthorized activity. As a precaution, we recommend customers follow security best practices, including enforcing MFA on privileged accounts, reviewing admin access, and rotating API tokens or keys where applicable.”
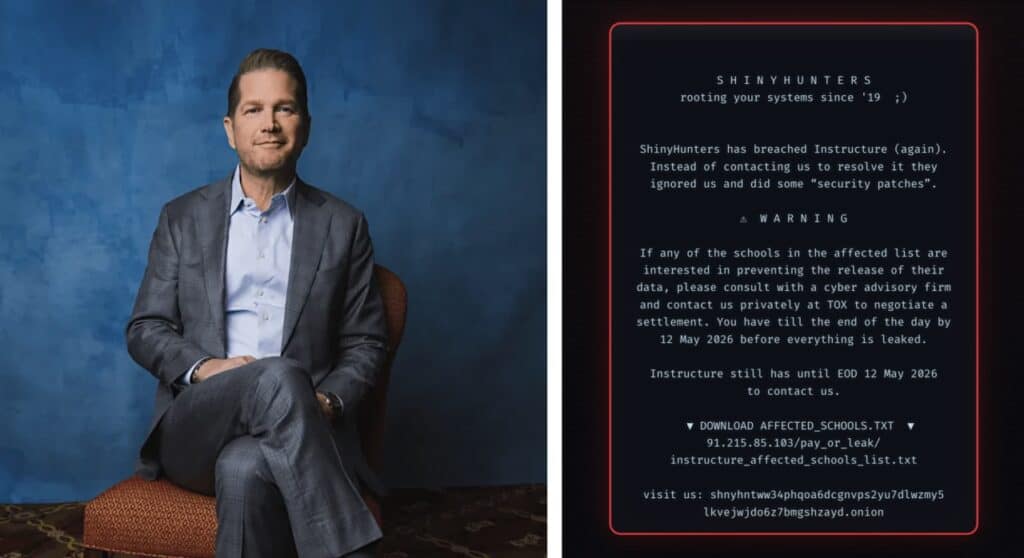
On May 07, the proverbial poop hit the fan.
A ransomware group, ShinyHunters, posted a hack notice on Canvas systems pointing out the pappyshow of a full week’s worth of empty promises by Instructure: “ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some security patches”
The graphic notifying Canvas users of the hack invited schools to review an online list of affected institutions and to make their own arrangements to pay a ransomware fee.
The deadline? May 12, 2026.
Instructure immediately shut down Canvas globally.
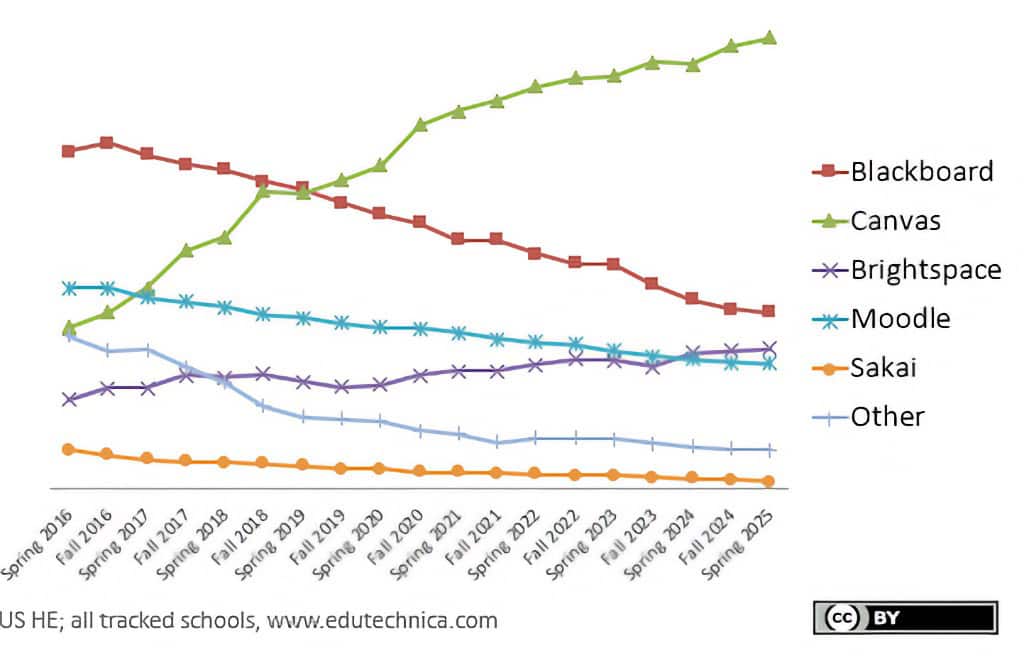
Canvas, which delivers an end-to-end hosting service, is used by half of all colleges and universities in North America.
ShinyHunters claimed to have accessed, in a 3.6 terabyte exfiltration, data affecting a wide swath of the 275 million users whose data has been captured by the platform (30 million are active users) and 9,000 schools that use the LMS globally.
Instructure’s response to the issue was unusually lax, particularly given that they had been targeted by ShinyHunters in 2025 when their SalesForce service was attacked.
On May 11, company CEO Steve Daly issued the following statement.
“We know that concerns about the potential publication of data related to this incident remain top of mind for many customers. We understand how unsettling situations like this can be, and protecting our community remains our top priority.”
“With that responsibility in mind, Instructure reached an agreement with the unauthorized actor involved in this incident. As part of that agreement:
The data was returned to us.
We received digital confirmation of data destruction (shred logs).
We have been informed that no Instructure customers will be extorted as a result of this incident, publicly or otherwise.
This agreement covers all impacted Instructure customers, and there is no need for individual customers to attempt to engage with the unauthorized actor.”
Instructure has not revealed what the size of the ransomware demand was nor how much was paid to secure this outcome.
It should be noted that ultimately, Instructure is depending, as does anyone dealing with a ransomware group, on the honesty of thieves and terrorists.
How do these issues affect Trinidad and Tobago, or more specifically, the University of Trinidad and Tobago (UTT) which was affected by a brief outage of Canvas services and deferred activities requiring the service for a week?
In response to questions, UTT’s Senior Manager, Corporate Communications, Sandra Ganness, responded that, “Canvas by Instructure is used by UTT as its Learning Management System (LMS).”
“UTT does not use Canvas as its primary authentication platform. User authentication is managed through the University’s Single Sign-On (SSO) environment, where multi-factor authentication (MFA) is enforced for institutional access.”
“The University also maintains established cybersecurity controls and continuously reviews its digital systems and security practices in keeping with operational and academic requirements.”
“The selection of a Learning Management System is based on a range of factors including teaching and learning requirements, scalability, support, reliability, cybersecurity considerations, integration capabilities, and total cost of ownership.”
“UTT adopted Canvas following a formal institutional review process and after previously utilizing Blackboard. Moodle was evaluated during earlier reviews but was not selected at that time based on the University’s operational requirements.”
“Like many modern universities, UTT utilizes a combination of internally developed systems and established external platforms, depending on the nature, complexity, support requirements and strategic importance of the service being delivered.”
I’m familiar with BlackBoard’s Collaborate, having taught using the platform for the two years of covid-19 lockdowns. UTT’s decision to drop Blackboard was mirrored by UWI’s St Augustine campus soon after the return to in-person teaching.
Higher education software is an unusual proposition that demands flexibility and agility in development to meet education needs that are more dynamic today than at any time in the last century.
Blackboard hit its inflection point relative to Canvas in the first quarter of 2019, when uptake of Canvas overtook declining use of Blackboard’s LMS.
The open-source solution, Moodle, continues to be an option, but Canvas now boasts more active users than its three closest competitors combined.
It is the gorilla in the room of higher education software and that beast has now been shown to be careless, having taken inadequate mediation and attack surface hardening after the 2025 incident and seems vulnerable, having paid for a likely cosplay of data destruction.
In the wake of the 2024 PowerSchool breach, that company paid a ransom, but that didn’t stop ransomware demands continuing as schools which used the Student Information System continued to receive threats to release their specific information.
The trove of user information from Canvas, is likely to be turned to use as a resource for improving the quality of phishing emails and used to power next level scams that make use of the names, emails and student-teacher messages that are believed to form the corpus of the exfiltrated data.
There are good reasons why law enforcement and cybersecurity professionals advise against trying to strike deals with criminals.
UTT’s stated response to the impact of the breach was: “The direct operational impact experienced by UTT was a temporary interruption in LMS availability for approximately four hours.”
“Although service was subsequently restored, the University took the precautionary decision to defer LMS-related academic activities scheduled for that day by one week to minimize disruption to students and faculty.”
“Relevant updates have been communicated through established internal channels and the University will continue to provide further information as appropriate.”
“UTT continuously reviews and strengthens its technology environment as part of its established governance and risk management processes. Independent of this incident, the University had already initiated a review for its Learning Management System through the Centre for Teaching, Learning and Instructional Support (TLIS).”
“That process remains ongoing. The University will continue to assess both internal and external technology solutions to ensure that systems supporting teaching and learning remain secure, reliable and aligned with institutional requirements.”
Blackboard, which has been in decline for years after its acquisition by Anthology has fought its way back from 14 months in Chapter 11 bankruptcy as a reset organisation with US$70 million in financing and a mandate to completely reassess its position in the higher education software market.
Matt Pittinsky, a co-founder of Blackboard went on to lead Parchment, an academic credentials management company, which was bought by Instructure in October 2023, placing him on the company’s board.
Pittinsky will take up his role at the rejuvenated Blackboard after a non-compete cooling off period. Phil Hill, who writes on Ed Tech, describes the whole dance that led to Blackboard’s return to competition.
Pittinsky would be crazy not to position the reemergent Blackboard as an alternative to Canvas staking the ground that Instructure has showed little interest in defending. His first mission will be to move Blackboard from legacy-product-in-decline status to becoming a contender in the space again.
Moodle, apart from being open-source, is also self-hosted and is starting to look like a viable contender to some universities stung by the data breach. The University of British Columbia deployed the open source software as a backup and alternative to Canvas in the wake of the breach, but switching would be a multi-year, wrenching prospect.
The formal public response of the 16-year-old company to two consecutive breaches of its infrastructure was, demonstrably, that of a cybersecurity neophyte with no real feel for its real-world responsibility to the education community it has so successfully courted.
The “deal” will probably stop dark web publication of the data cache that ShinyHunters exfiltrated, but only a fool would proceed as if that data was actually destroyed.
Instructure has handled the entire incident, beginning with its first understanding of a vulnerability on April 29, like a software vendor trying to manage a hack and fumbling it badly.
But the company is managing a very different proposition than most software vendors do. It has positioned itself as an education partner, managing a wide range of integrations with education software tools, presenting its services as a seamless integration of pedagogy and digital engagement.
When students found themselves locked out of their educational software during an exam week, when the company suffered the most extensive ransomware hack of an education software system on record, it chose a very different voice. It fell back on service provider speak.
To date, Instructure has not explained the details of its “deal” with ShinyHunters. It has offered only platitudes to its customers, discussing the issue in the vaguest possible terms while its cybersecurity was clearly in a state of major compromise, wasting fragile trust on counterclaims about the size of the exfiltration while demonstrating little affinity for the reality of schools locked out of the virtual backbone of their teaching systems.
Instructure has been good about parroting all the current doublespeak about the future of education, but when it counted, the company was mute about the integrity of the systems it asked millions of students to trust.