- Deepfakes, created using AI to mimic real people, pose a significant risk to businesses, with at least 26% experiencing attacks.
- Studies show that people struggle to distinguish between real and fake content.
- To protect against deepfakes, organizations should expose their employees to a range of deepfake examples.
Above: Deepfake concept image. Illustration created using the Flux model on 123RF.com
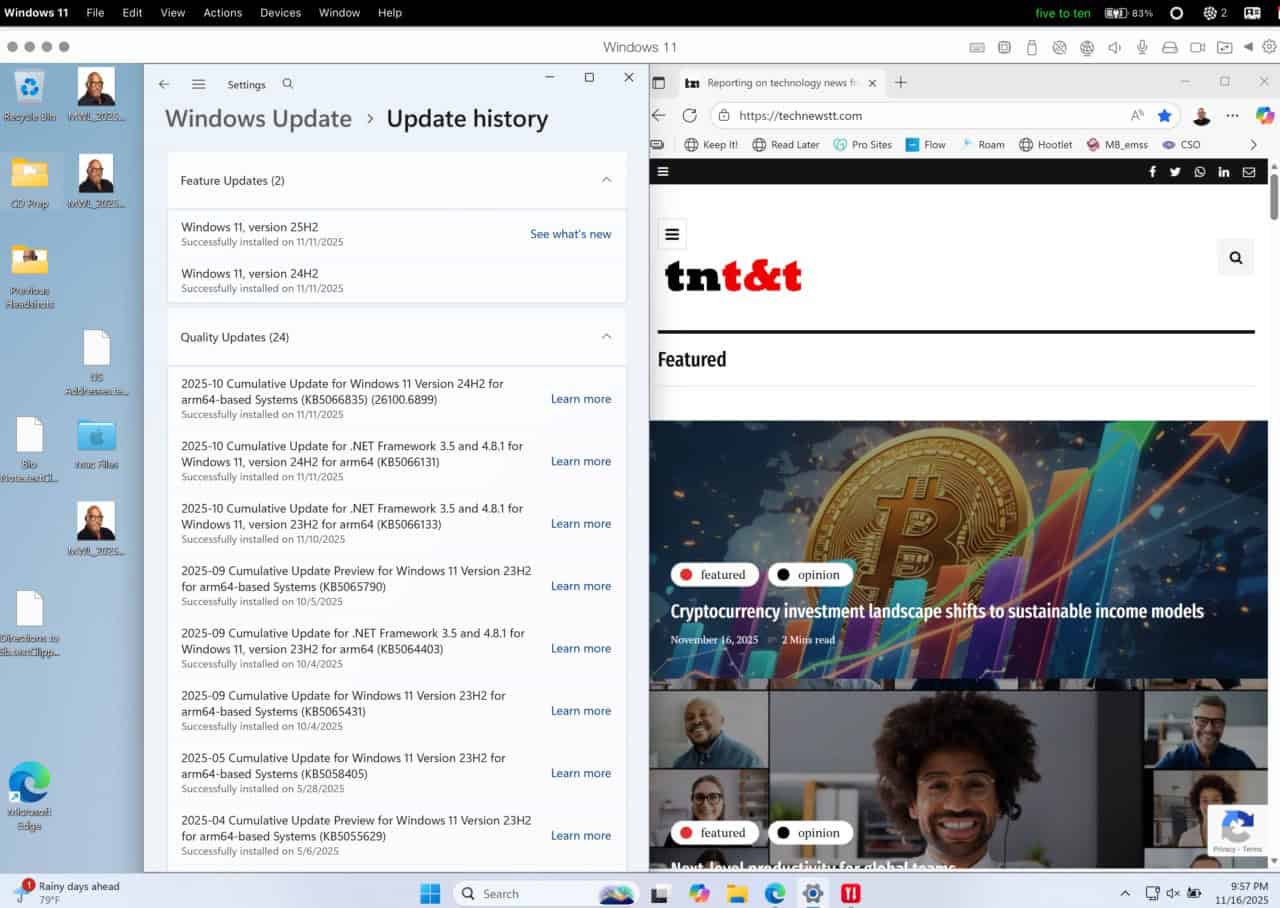
BitDepth#1516 for June 23, 2025
When the conversation turns to the impact of AI on society, the strip-mining of intellectual property by Large Language Models (LLMs) and the impact on future jobs tends to dominate.
Much of what’s at stake in the future of artificial intelligence development is nothing less than a shared understanding of what is true and what is not.
Nowhere is that being put to the test more dramatically than in the rapidly advancing field of deepfakes, which use AI technology to map facial characteristics and voice patterns then use that information to create increasingly convincing facsimiles of real people apparently saying real things.
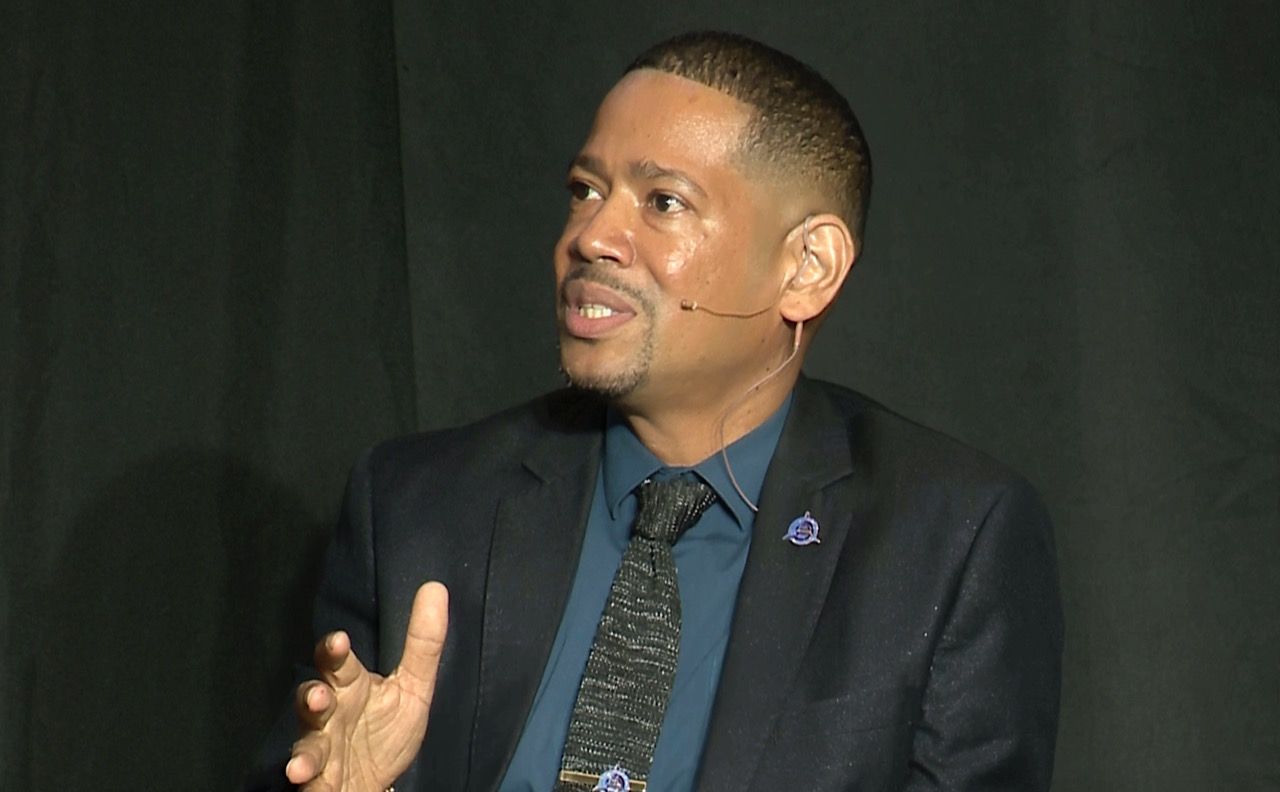
According to Perry Carpenter, chief human risk management strategist of KnowBe4, a cybersecurity investigation firm, the risk to companies is real.
In a recent online webinar, he referenced a Deloitte study that found that at least 26 per cent of businesses are experiencing deepfake-related attacks, a number that is set to rise sharply.
The era of casually dismissing deepfakes is definitely behind us. Carpenter notes that studies assessing the ability of focus groups to pick deepfakes from original media discovered that 80 per cent of the time, participants picked incorrectly, despite being primed to look out for falsehoods.
“I think we’re already past the time that anyone will be able to reliably tell what is real and what is not real when it comes to voice and video, when it comes to imagery, and then we’ll not be able to tell what’s real or AI generated when it comes to text,” Carpenter said.
“We all see tells for those things right now, but again, those may be artifacts of the past or they may be artifacts of a lazy attacker.”
“As security people and as people who think about this a lot, we usually [think of] nation-state or APT (Advanced Persistent Threat, nation state attack) level of thinking when it comes to creating these types of attacks. There are very few of those APT level attacks but there’s are a flood of [deepfakes that are] very effective and are tricking people today.”
“When you’re starting to find ways to inoculate your people to this through simulations or through awareness exercises, you need to give them the full range. They need to see the bad stuff. They need to see the scary stuff, and they need to see the nation-state level stuff, so that they see the spectrum.”
But deepfakes on their own, while persuasive, depend to a great deal on context. How they are used and implemented to influence thinking or urge action, whether it is political persuasion, sharing sensitive company information or just weaponising defamation of character.
Carpenter argues that the narrative framing and targeting of deepfakes is as important as the improving technology that generates them.
He outlines four steps that everyone should take and, I’d argue, journalists must take before accepting information delivered by provocative videos or acting on unusual phone calls, which he describes as the FAIK framework for evaluating these messages (book available here).
F Freeze & Feel.
A Analyze the Narrative & Emotional Triggers.
I Investigate (claims, sources, etc.)
K Know, confirm, and keep vigilant.
Specifically, he encourages netizens to cross-examine online media snippets by asking why the message exists, what’s the story it tells, who benefits from the story’s distribution and what the goal of sharing might be.
Deepfakes have been used in recent elections globally. There was even one in TT’s April election which altered Mrs Persad-Bissessar and Roger Alexander’s greeting after his onstage political introduction to manufacture a fake kiss from the footage.
A 2018 BuzzFeed video faking a Barack Obama address (link.technewstt.com/fake) was state of the art then, not anymore.
Expect more of this kind of thing to play a part in political jousting, cybersecurity infiltrations and general muddying of the waters of fact in favour of agenda-driven fiction.
The tools are becoming more powerful, are more widely available and accessible and are becoming simpler to use.
With a sufficiently powerful computer system, it is already possible to do live deepfakes, contemporaneously replacing the face of a live speaker with a deepfake mask that matches their movements and expressions while altering voice to match previously sampled vocal patterns.
This is now.
With the reliability of truth crumbling in real time, the need for greater awareness of these pervasive digital deceptions is growing exponentially greater, and a commitment to reporting truth in the face of persuasive and widespread falsehoods may be the last great differentiator for journalism.
The UNESCO Artificial Intelligence Policy Roadmap for the Caribbean.


































[…] Caribbean – When the conversation turns to the impact of AI on society, the strip-mining of intellectual property by Large Language Models (LLMs) and the impact on future jobs tends to dominate… more […]