Illustration by ingka.j.jiw
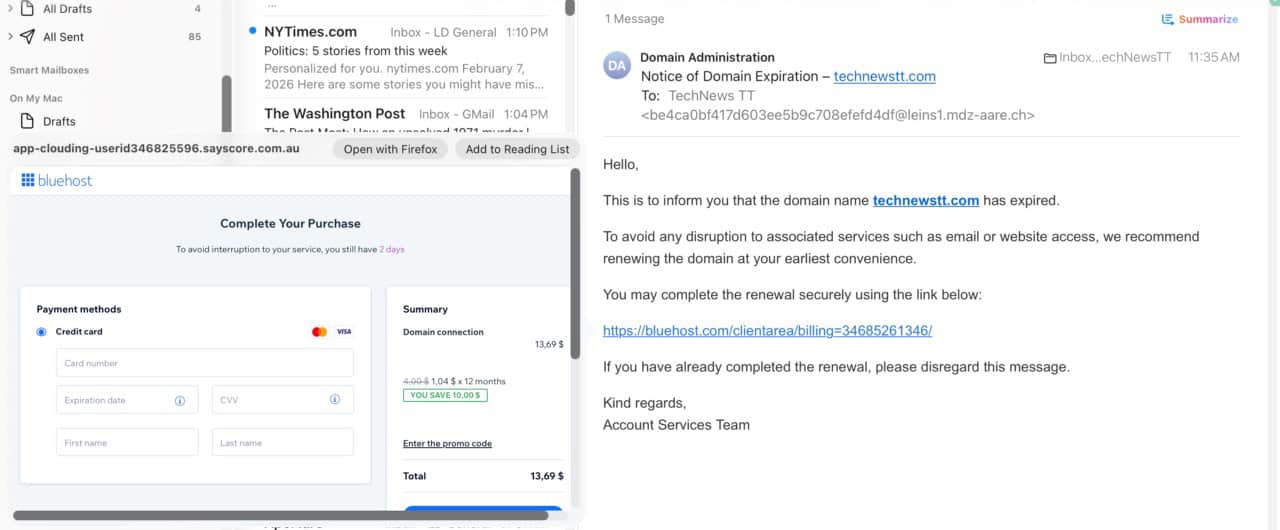
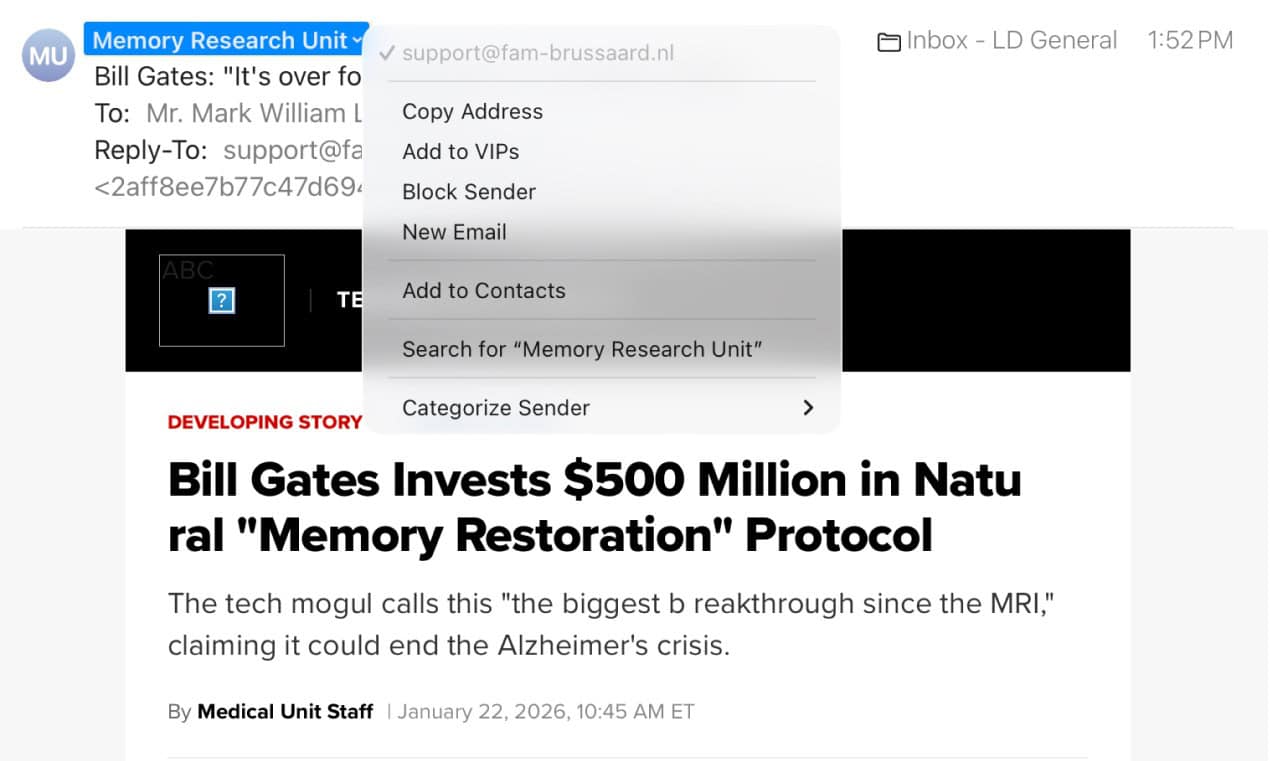
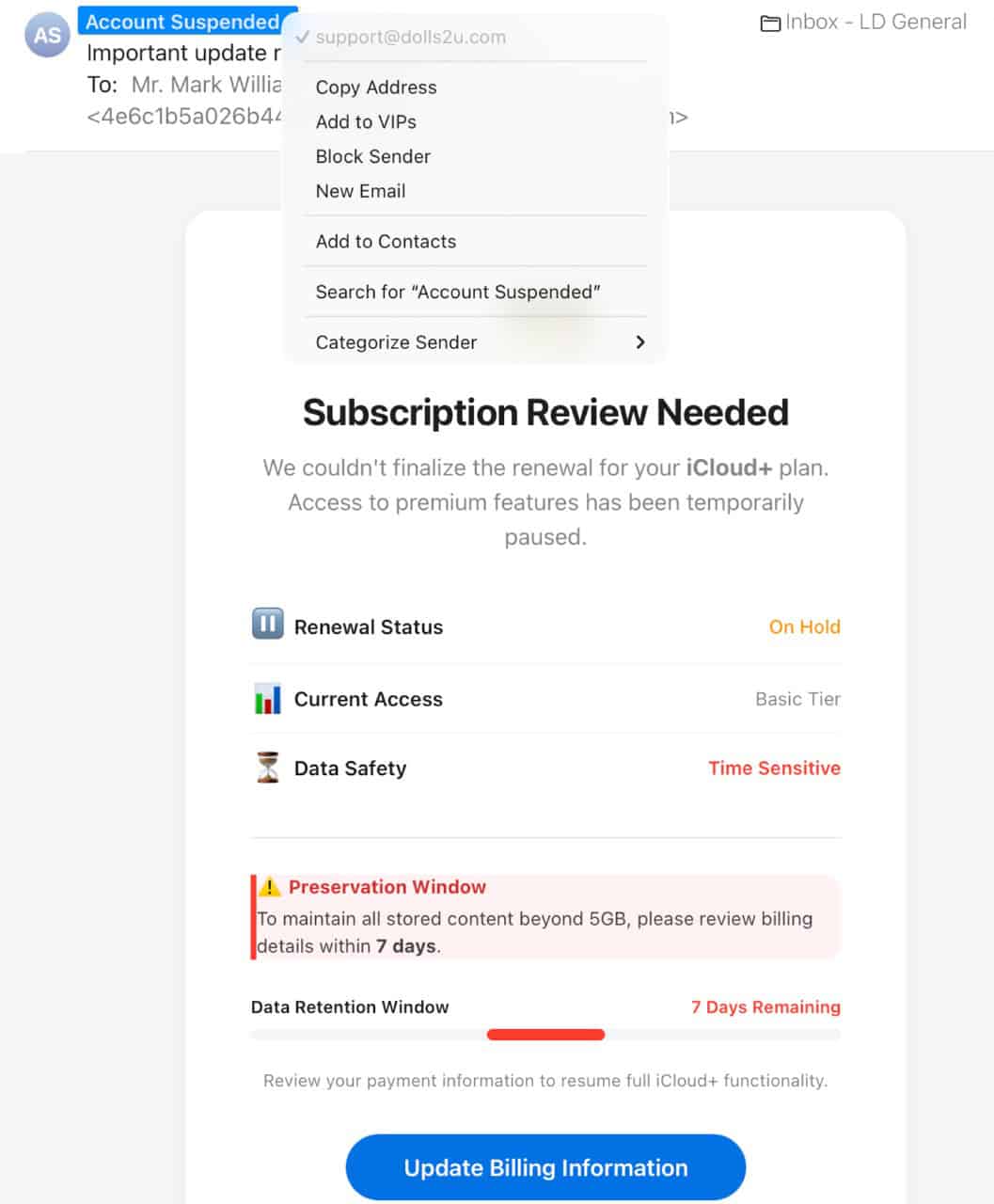
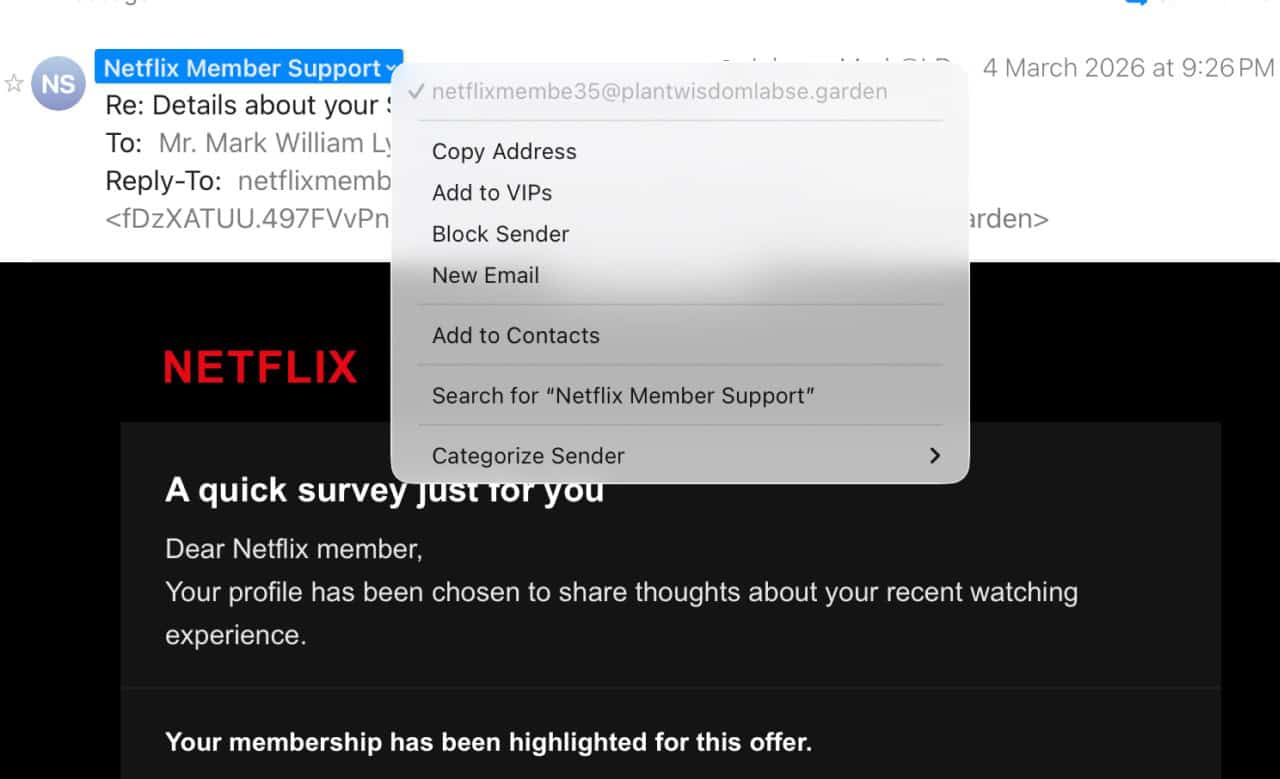
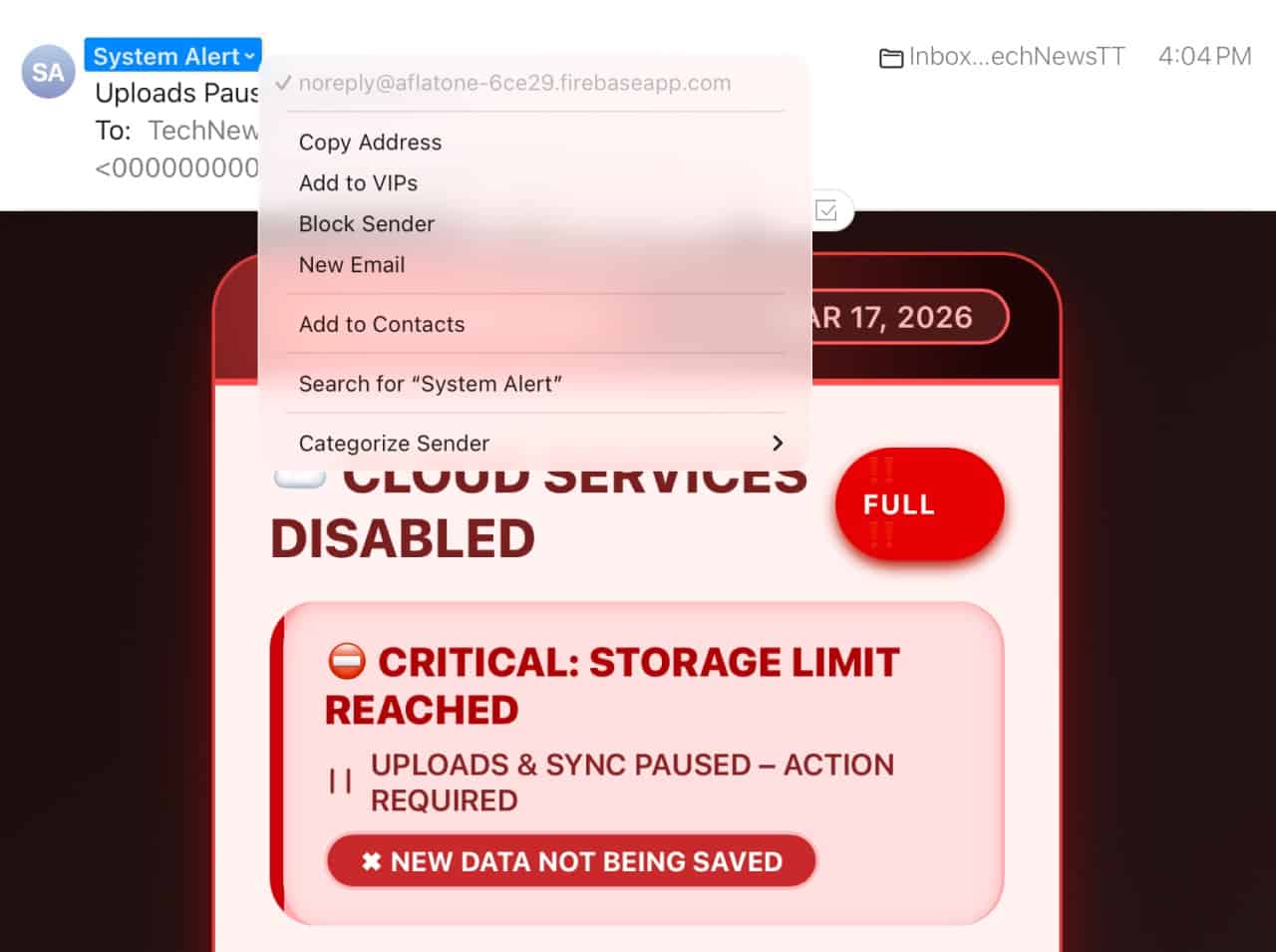
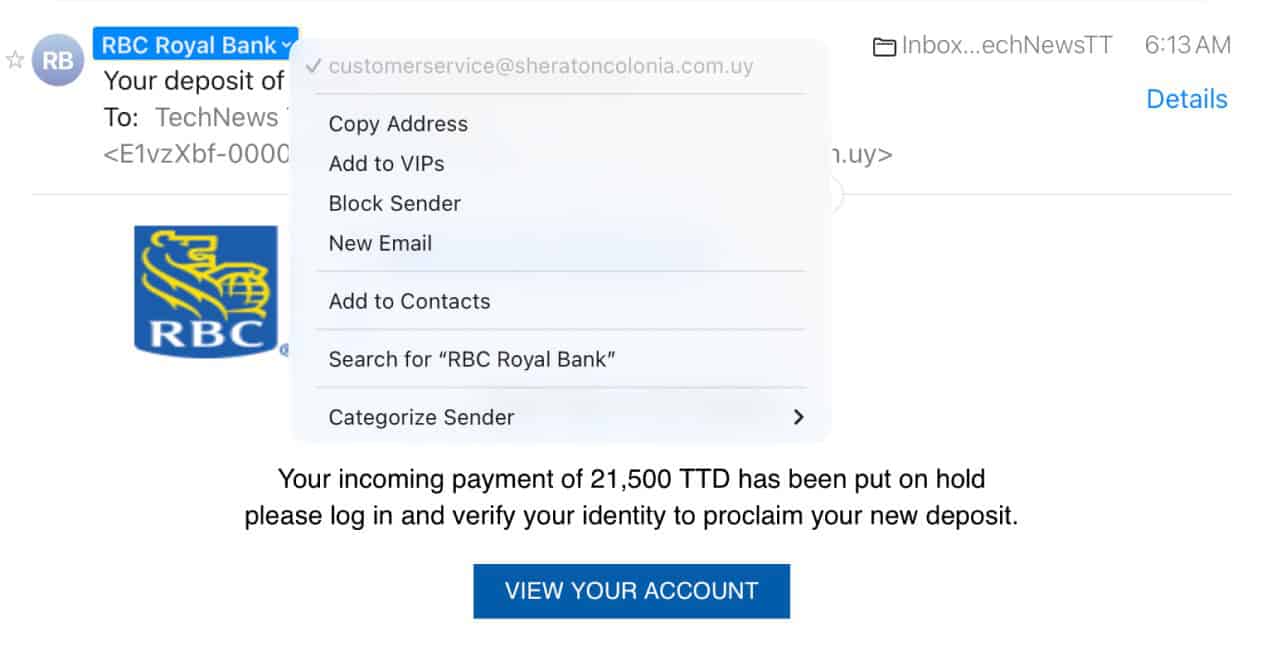
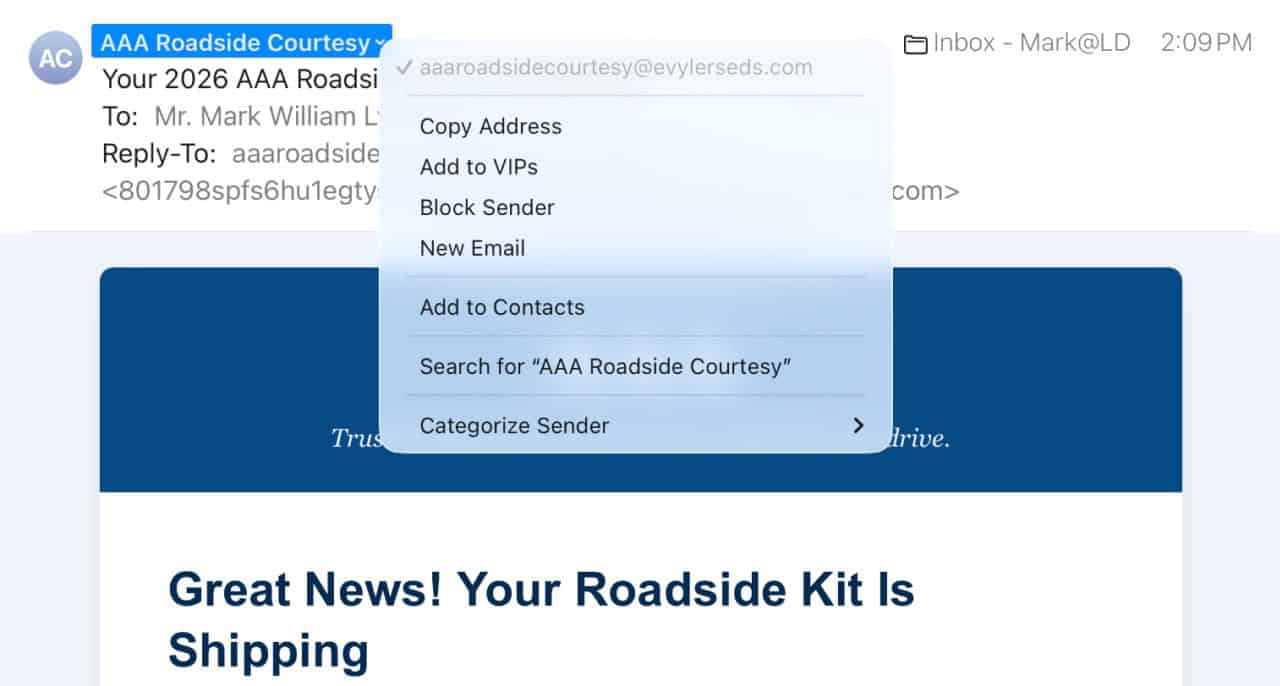
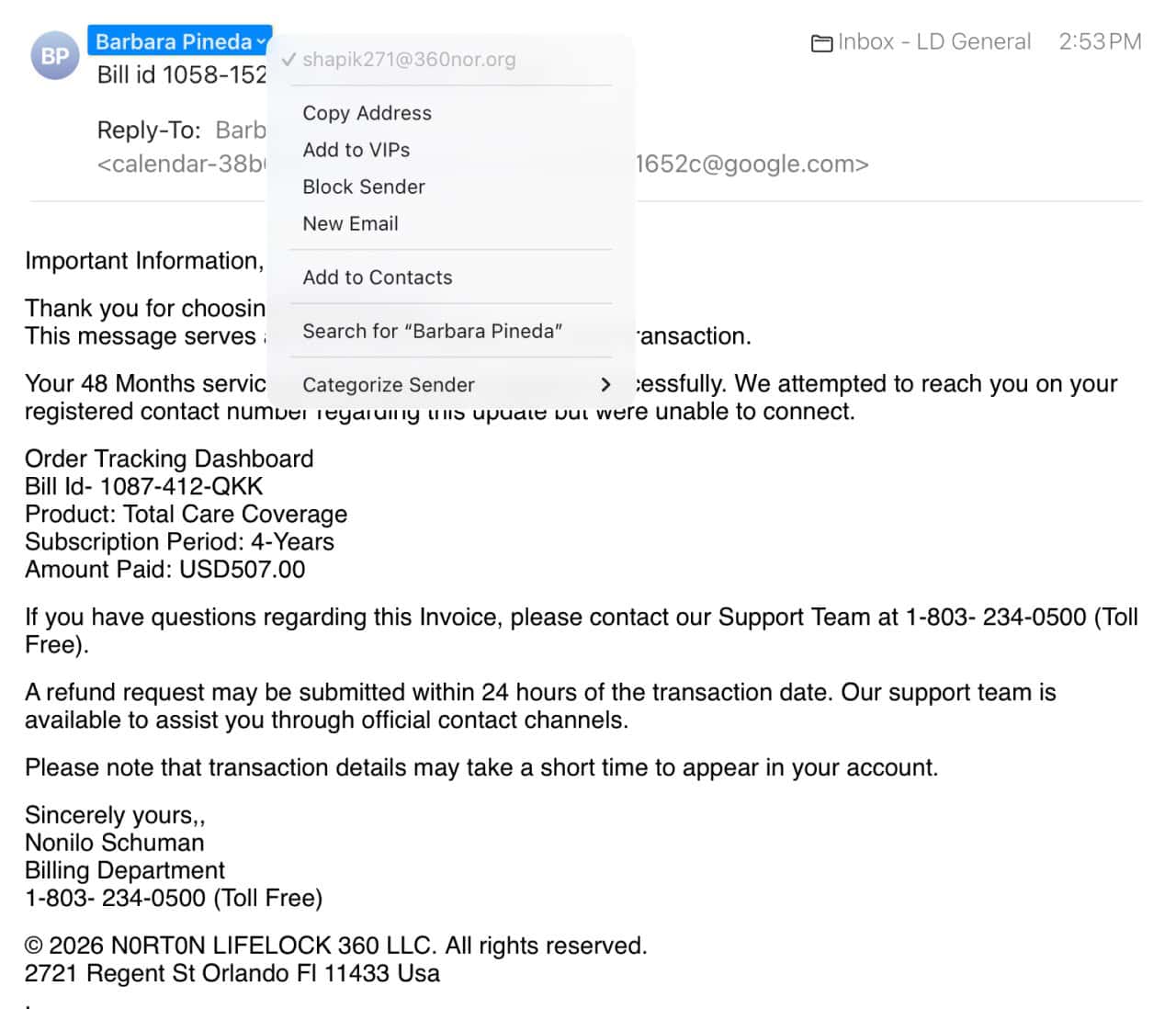
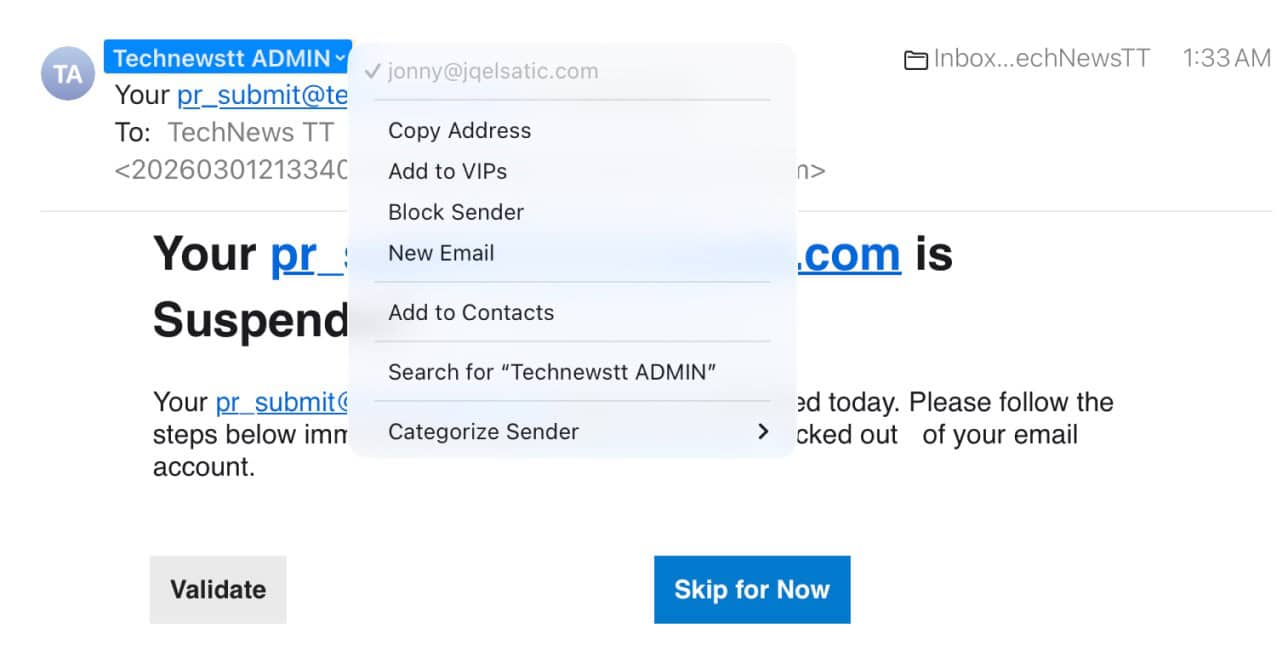
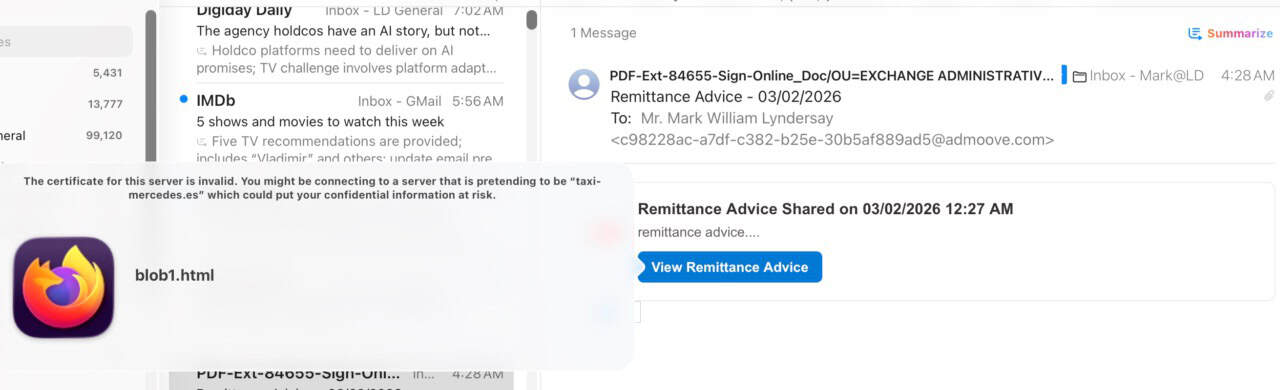
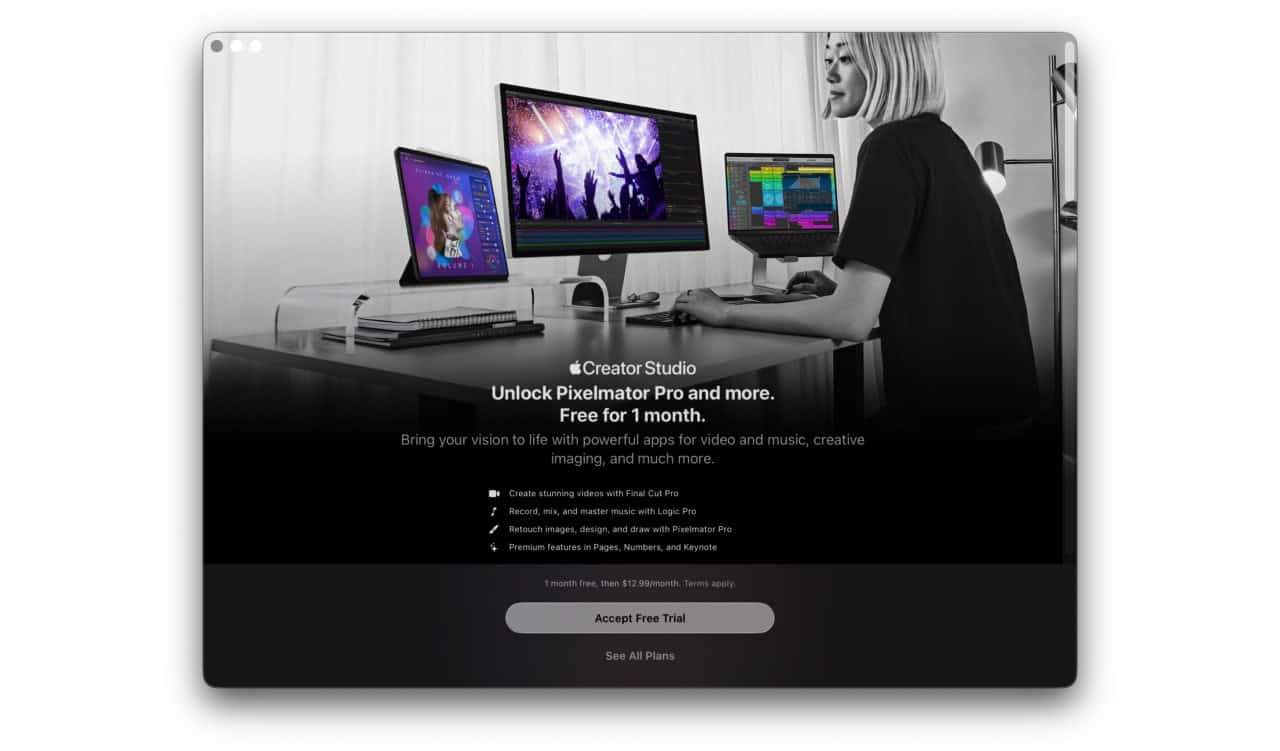
These are a collection of scam emails gathered over the last couple of months. The frequency and sophistication of these efforts to gather personally identifiable information from the unwary has been startling. Email graphics are becoming more convincing. Calls to unfortunate action are far more crafty and ways of disguising real destination URLs and sender emails require special attention to uncover.
Some of these blanked scam emails will obviously not apply to you, but senders are getting smarter about using generalised information about individuals and regions to craft emails that are more effective in targeting the unsuspecting.
The blanket rules continue to apply. Do not click on links before fully investigating them. Do not call given phone numbers, because AI tools are harvesting voice patterns. Do not respond to any email that seems odd.
If an offer is presented by a company you have never had any contact with offering something special consideration, it’s unlikely that you have been fortunate.
Go to the official websites of any service or business you deal with and make your queries there as a first step. The oldest rule of all still applies. Nobody gives anything away for free. Nobody has any money to give you.
Click on the plus sign on any image to enlarge.