- • Trinidad and Tobago introduced an online system for collecting traveler information on arrival and departure
- • Immigration data is crucial for national security, identifying overstays, and improving travel safety
- • The failure to address key data protection questions highlights the need for greater transparency and accountability
Above: Illustration by wafi99d/DepositPhotos.
BitDepth 1554 for March 16, 2026
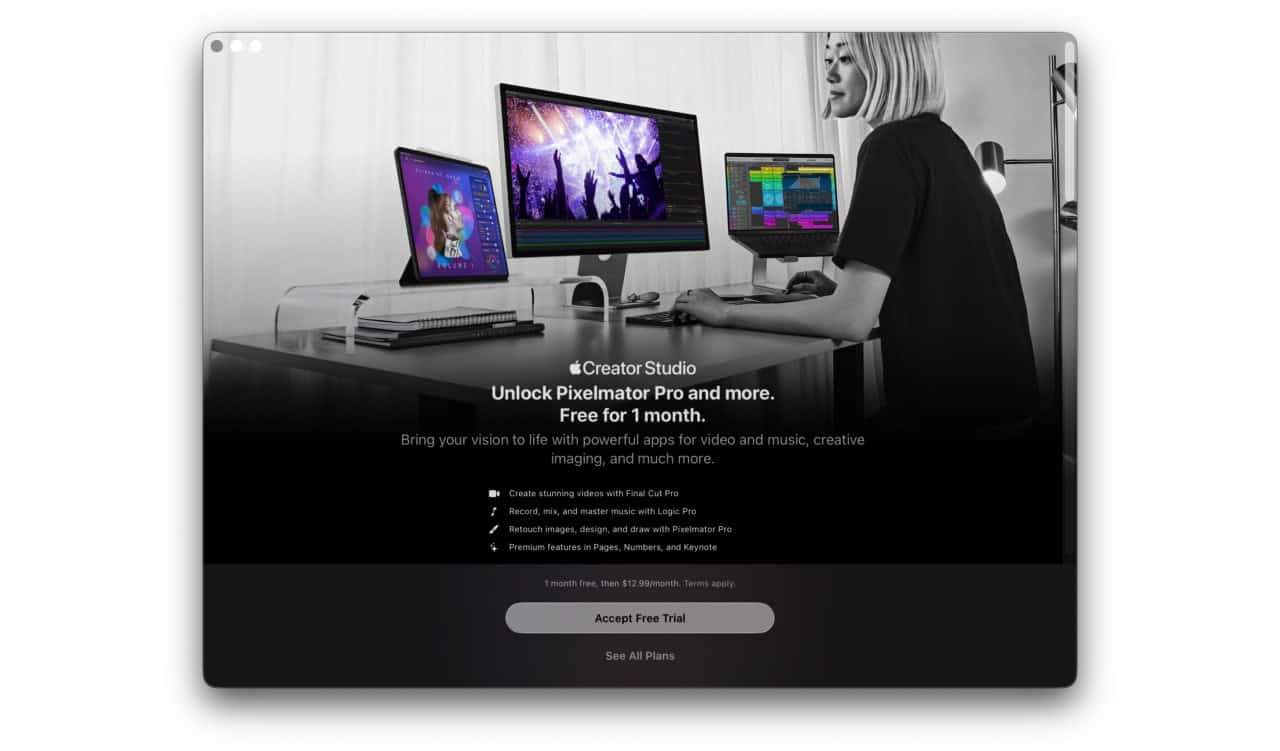
On March 11, 2026, the government announced the introduction of an online system for collecting traveller information on arrival and departure at ports of call in Trinidad and Tobago.
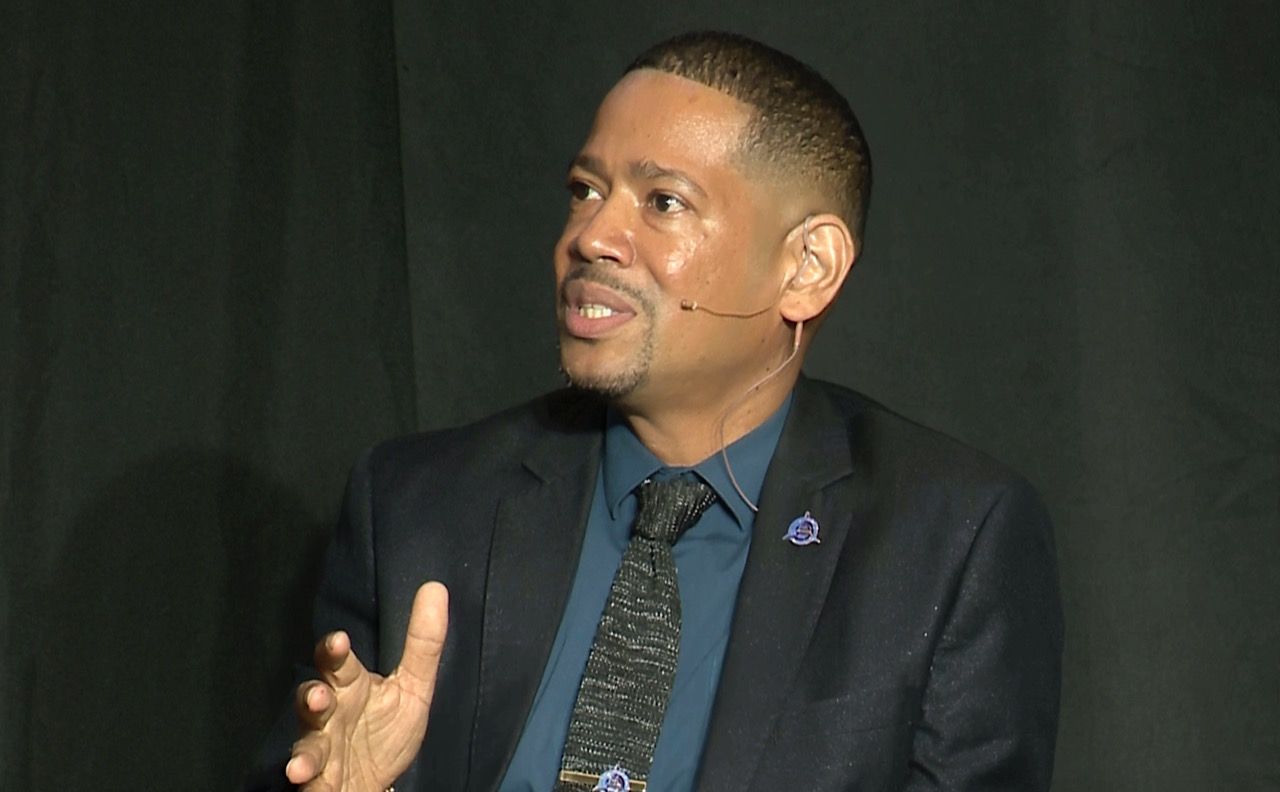
Minister of Homeland Security Roger Alexander claimed that, “We have created somewhat of a history today from where we were.”
Where we were was the absurdly outdated foot-long form that visitors had to fill out to submit information about their arrivals and departures at ports of call.
It is, however, incorrect to state that this online effort was the first attempt to digitize that process. An earlier effort in 2018 collapsed within a year after the introduction of seven automated arrival kiosks, wasting millions in taxpayer money.
Shuttered over contractual issues, neither the exact cost, the issues that caused concern nor the liability undertaken by Trinidad and Tobago in that deal was ever disclosed.
Meanwhile, the world moved on, improving systems that not only gathered traveller information, but also managed that data to verify authenticity and identify potential bad actors.
Every sheet of paper reluctantly filled in on entry into this country was a lost opportunity to join the rest of the world in verifying the authenticity of travel credentials and the identity of legitimate travellers.
This data wasn’t being collected simply to annoy visitors in immigration entry lines, though it did an admirable job of that.
Immigration data is used to improve national security, identify overstays and generally make travel safer.
Globally, Advanced Passenger Information (API) and Passenger Name Record (PNR) data is synchronised to limit the permeability of borders and to track the movement of travellers to identify potentially worrying patterns.
The use of advanced biometrics and pre-screening ensures that low-risk travellers have a smoother experience. Citizens using pre-screening systems like the Global Entry system breeze through the immigration process.
Clearly any system that gathers this information in advance, verifies it quickly and reduces roadblocks for regular travellers is a good thing.
The TT immigration form was a wall of bureaucracy that everyone had to climb, even if they moved through local ports so often that they knew officers on duty by their first names.
Piles of paper are a terrible way to access information and for most of the last few years, the form appeared to be a kind of receipt to back up information already available to immigration officers on the computers in their booths.
Addressing the change to digital capture, Public Administration Minister Dominic Smith dismissed concerns about data leakage archly, responding to a direct question about data security with a spurious comparison.
“You might be aware information has been available in paper-based format as well. Why hasn’t that been leaked?”
Given that this particular head table included the Homeland Security Minister, whose entire persona is built around street smarts and the AI Minister, positioned as a savvy tech bro in leadership, this response falls rather unfortunately into a disturbingly deep valley of wilful ignorance that should have been bridged more capably by both ministers prior to this press conference.
Paper forms offer the security of disorganisation and volume, something thats not an issue for digitally collected information.
Rishi Maharaj, Chief Executive Officer & Principal Consultant of Privicy Advisory Services noted that, “Comparing a paper form to a centralised online immigration database is a distraction.”
“A single digital breach can expose hundreds of thousands of records simultaneously to a remote attacker anywhere in the world, something physically impossible with paper. The minister’s claim that paper has never been breached is also not a verifiable data protection argument, since T&T has no mandatory breach notification framework that would compel disclosure if it had been.”
Much was made at Wednesday’s press conference about the government’s efforts to amend the Immigration Act to allow for digital data collection and more recently, a Memorandum of Understanding (MOU) between the Homeland Security Ministry, the Telecommunications Authority, the Public Administration Ministry and the TT Cyber Security Incident Response Team (TTCSIRT) was announced, promising to improve cybersecurity under a collaborative “One Government” approach.
These efforts are being pitched, if the press conference on Wednesday was any indication, as indicative of “good governance” directed to relieve citizen “pain points.” That’s not even getting into the absurdity of the government announcing an MOU with itself.
To be clear, any lubrication of the travel process is an advance. The technocrats present were at pains to note that this is a system in development, which will be critical to any effort to usefully link it to any international databases.
But before we even get to there, Dominic Smith needs to reverse his “we know what’s good for you” approach to data privacy. That hasn’t worked well in the past.
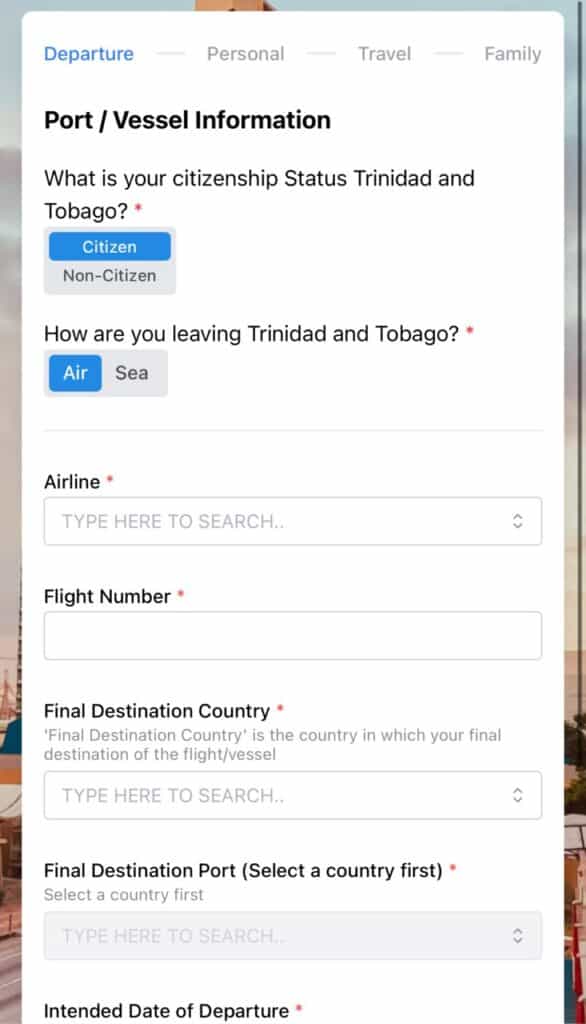
The government will not only be collecting personally identifiable information (PII) on its citizens, it will be harvesting PII from the citizens of countries visiting Trinidad and Tobago.
Many of those countries have hard rules about how that kind of data can be handled. The EU’s GDPR is particularly strict about issues like data retention, data use transparency and user accessibility.
“The minister should have been able to state the retention period, the encryption standard, that a Data Protection Impact Assessment (DPIA) was conducted, and what the breach notification procedure is— he answered none of those four things, and citing TT-CSIRT engagement and an MOU with a regional law enforcement body speaks to process, not protection,” Maharaj said.”
As a baseline, a privacy notice to let individuals understand what data is being collected, the legal reasons, retention period, security to protect data and a contact for any questions should have been a starting point for this data collection process at launch.
“Long-term retention of immigration data is not recommended unless there is a clear, lawful purpose beyond the original processing. Retaining a large centralised database of passport numbers and travel histories indefinitely without that justification compounds risk by creating an ever-growing target for exactly the kind of ransomware and exfiltration attacks that have become routine in the Caribbean since 2020.”
As a reminder of what is publicly known about data breaches in TT since 2020, consider this ignominious history of incidents and the deliberate attempts to obscure information about these breaches and the still unknown level of exposure of customer PII.
Despite official evasion and denials, PII from local company and government data dumps has been identified as being sold in dark web marketplaces.
- ANSA McAl, 2020
- Port of Spain City Corporation, 2020
- Paria Fuel Trading, 2022 (Phishing)
- Massy Stores, 2022
- TSTT, 2023
- AGLA, 2023
- NIBTT, 2023
- SWHRA, 2023
- Courts, 2023
- PriceSmart, 2023
- Blue Waters, 2023
- GovNeTT, 2024 (Phishing)
- Venture Credit Union, 2025
Between 2019 and 2023 alone, TTCSIRT reported 203 breaches.
The overwhelming majority of these cyberattacks, along with their consequences for customers and users of their services, has never been publicly revealed.
There is no government agency that advocates on behalf of citizens for public disclosure of data breaches in Trinidad and Tobago.
This is an environment in which there has been widespread infiltration of local networks and harvesting of vast swaths of customer data in leaks that have been independently identified on the dark web.
In the face of clumsy counter-narratives, Mr Smith and Mr Alexander are leaning on a rusted banister hoping for reflexive support and trust for new data collection initiatives.
Citizens simply have no good reason to trust local businesses or the government.
Despite claiming to have taken a superior position to their predecessors, the new government has made no tangible commitment to delivering real world protection of the public’s PII.
This data collection solution has been developed by a “regional vendor,” one who remains steadfastly unidentified, at a cost that the government apparently has no interest in revealing for spurious and undefined “national security” reasons.
- Is this a licensing arrangement?
- Are we renting software and not developing it locally?
- Will this, like other abandoned digital rentals, become a financial pain point eventually?
- Who are the architects, advisors and professional technocrats involved in this process?
“Experts and professionals” are broad descriptives, not specific identifications of people and actual, proven expertise.
The public does not and should not trust vague promises, only hard action that demonstrates a commitment to real world transparency and responsiveness to citizen concerns about how their PII is handled and by whom.
“The right to privacy or private life is a right guaranteed under Section 4 of the constitution,” Maharaj said.
“ Data Protection laws provide guardrails in how government and business collect and use that data. I think the legislation has stalled because the government and interested parties don’t want to be regulated in how they use personal data and to be held accountable for it.”
This is a list of questions, some from Jarrod Raymond (@RebirthofProf on X) and others from Rishi Maharaj that the press conference should have been ready to answer on day one.
- How long will an exit/entry submission be kept after the event?
- Which other government agencies will have access?
- Where will this data be stored (location on the globe)
- Can we request [a full transcript of retained] records?
- What is the procedure if my data is breached, would I be notified? Travellers are entitled to know whether they will be notified, by whom, within what timeframe, and what remediation will be offered.
- Will this data be shared with foreign governments or regional bodies? The CARICOM IMPACS MOU the minister referenced makes this a live question, not a theoretical one. Data flowing to a regional law enforcement network implicates sovereignty, third-country transfer rules, and rights enforcement.
- Was a Data Protection Impact Assessment conducted before launch, and is it available for review? A system of this scale and sensitivity should have had a formal DPIA. The public has a legitimate interest in knowing whether privacy risks were assessed before deployment, not after a problem arises.
Despite their earnest claims to be doing better on the public’s behalf, ministers Alexander and Smith are doing exactly what their predecessors did, asking for trust without offering any foundation on which it might reliably be placed.