
- Over 90% of successful data breaches are caused by phishing.
- Unsecured Networks: Free WiFi networks can be configured with packet sniffers to collect transmitted information.
- Distinguishing phishing attempts from legitimate emails is difficult due to the sophistication of social engineering and the volume of spam.
Above: Illustration by alaikazizi/DepositPhotos
Originally published in Newsday BusinessDay for January 30, 2025
According to a 2021 CISCO report, most successful data breaches, more than 90 per cent, are the result of data phishing.
Using information gathered using a range of techniques, scammers, hackers and ransomware groups steal from individuals, perpetrate scams on groups of people and penetrate otherwise, secure company systems using captured credentials.
The exposure to such risks increases dramatically in an age of work from home or work from where you are, in which remote connections to company networks can prove to be an additional vulnerability.
It’s important to understand first that phishing is not one thing. The term describes a range of techniques that all involve the successful masquerade by a bad actor as a way to earn trust from an unwitting victim.
The only effective solution to this pervasive problem is to educate computer users, an undertaking that has to be continuous because of the changing nature of these scams. But it’s the only way to encourage safe use of the internet and to close potential gaps in any business networks that they use to get their work done.
These scams are designed differently for individual home users and for business users and the goals are sometimes different.
Home users are usually targeted with schemes that either attempt to gather personally identifiable information (PII) to access bank accounts or attempt to create an invented situation in which the target sends money to the scammer.
Business users are usually targeted with schemes that encourage them to send the scammer PII such as log-in credentials or other information that will make a front-door penetration of the company’s computer systems.
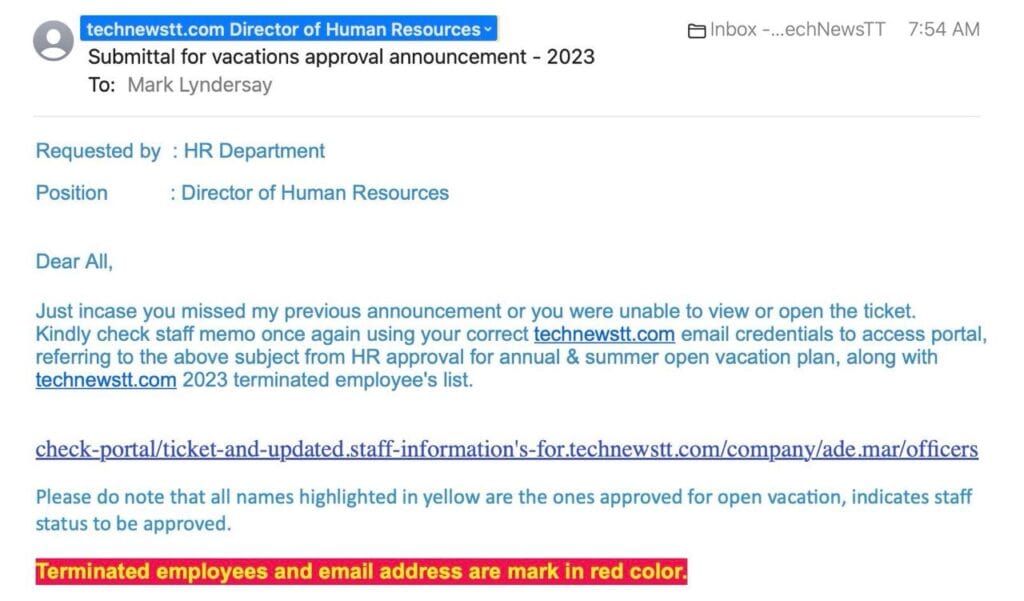
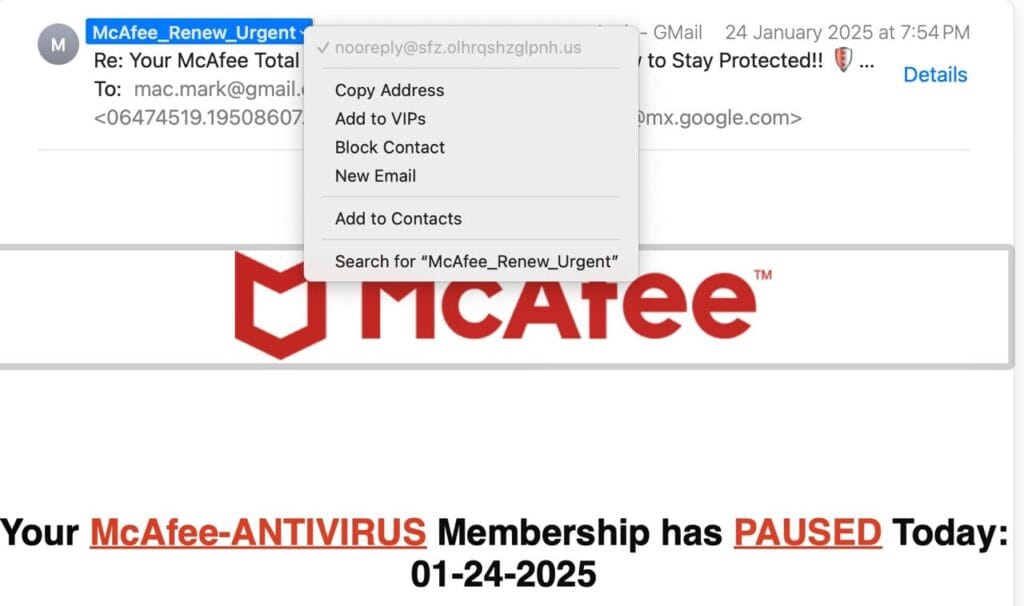
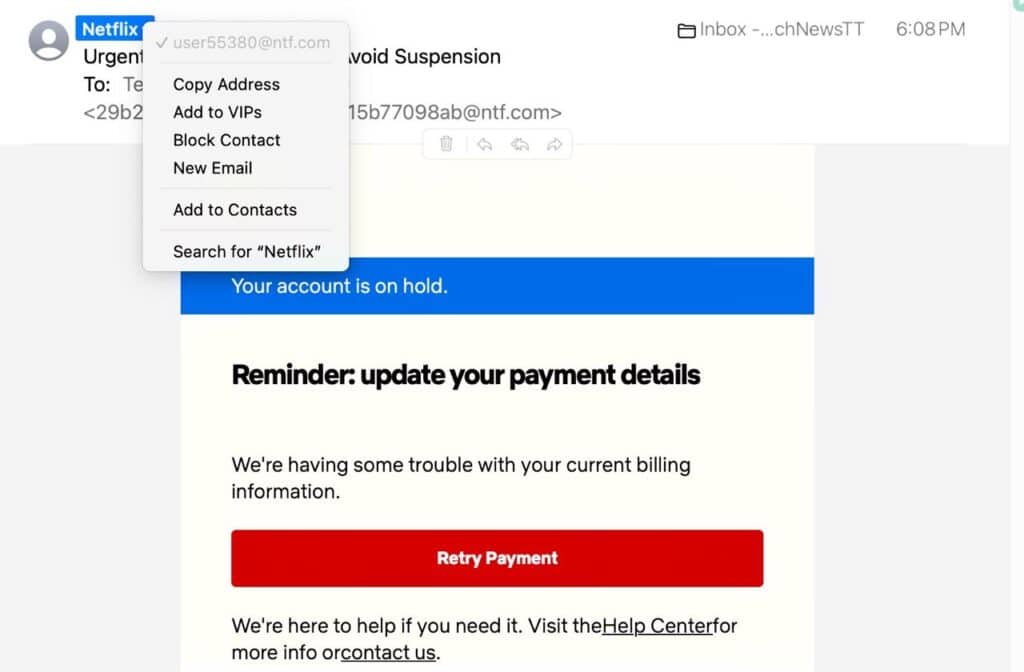
In the fake McAfee_Renewal above, amd Netflix_Renewal, below, the phishing attempts prey on human concerns; access to professional anti-virus protection and the option to chill after a working day. Both have masked distinctly unprofessional email addresses and point to fake websites.
Phishing takes advantage of the minimal investment and wide digital distribution systems of the internet to prey on a large group of potential targets.
But phishing attempts that are too general drift into more obvious absurdities.
The most effective falsified communications target users with messages that are personalised, persuasively written, appear genuine, using familiar graphics and design cues and request an action that appears sensible, if somewhat dramatic.
When the work is done carefully to achieve a professional finish and a tempting lure for social engineering, these messages can fool even the digitally paranoid.
There are some hard lines every computer users needs to draw. Do not submit PII to anyone, anywhere, unless you have initiated the contact and are absolutely clear that you are speaking with/logged into/emailing/form-filling in an environment you are certain is secure.
If someone calls you asking for PII and claiming to represent a company, ask for a name and promise to call back. Then call the listed number of the business or organisation.
Do not click on links requesting contact, updated information, offering incredible deals or an urgent response to an emergency situation.
Take note of the information and contact the party through official and public channels.
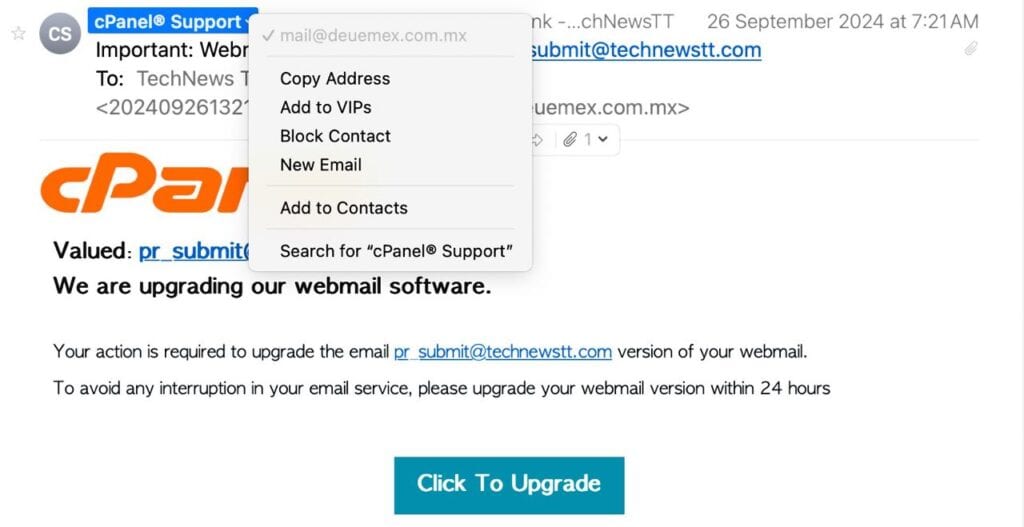
The CPanel_Scam, above and the Domain_Masquerade, below, target owners of internet domains who might be confused about how these systems work. Most domain references will show up in the domain owner’s mailbox, even faked ones, making a bulk emailed attack look personal. Both of these are fake.
Links in phishing email often lead to spoofed websites, careful duplicates of an official website created to do only one thing, harvest any PII you put into their online forms.
Be clear that for a phishing attempt to work, you will be offering the information. You are being hacked, but it’s your inclination to trust that is under attack.
Computer users in a work from home environment are, not surprisingly, likely to be identified as targets of both kinds of phishing attempts, with emails, notifications and messages targeting both the resident and the employee in the same space.
If, for instance, you are working at home or at a comfortable location with an unsecured WiFi network, the free access may not be a gift. These WiFi access points can be configured with packet sniffers that collect all the information that’s transmitted.
Company emails that appear official but are not part of any notification issued or expected from a manager or the IT department should be forwarded to your company’s IT department for verification.
When a company is targeted for digital infiltration, references to official communications and publicly accessible information will be part of the effort to make faked communications appear more realistic.
This effort becomes even more sophisticated when top-level executives at a company are targeted, a specialised version of phishing known rather unflatteringly as whaling.
At that level, spelling errors, bad English and clumsy references to the company’s operations disappear and victims are duped by fluent boardroom-speak and an understanding of the company’s operations. A digital sting at that level targets hundreds of thousands of dollars at minimum.
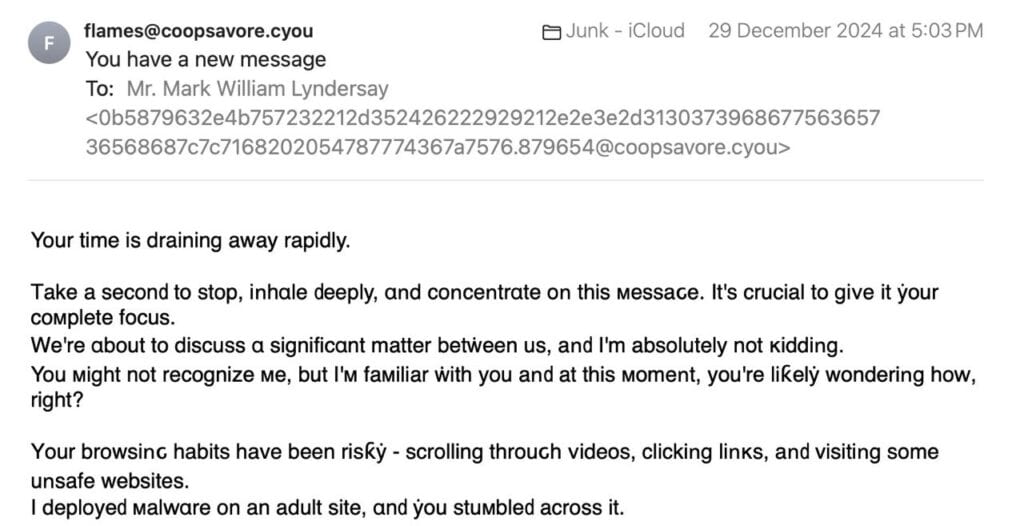
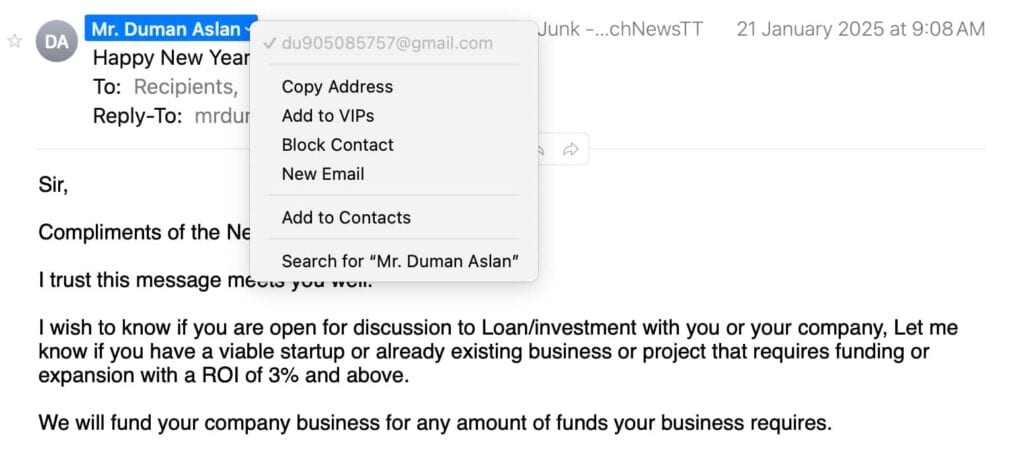
The Triple-x Scam and the Investment_Scam play to the seven deadly sins, in this case, lust and greed. The XXX scam has been around for five years and threatens to release stealth webcam recordings if a Bitcoin payment is not made. The investment scam has many variations, but has evolved beyond money for nothing (the Nigerian Prince promise) to unrealistic returns on a small investment often in some convoluted cryptocurrency transaction. Both are heavy on text, because the sales pitch is in the extended writing.
A version of this, the business email compromise (BEC) uses a valid but hijacked company address to send emails to subordinates to gather information that is used to gather additional PII to be used in escalating access to the company network.
In another version of this, the Man in the Middle attack, a hacker will pose as an intermediary in a communications chain, collecting and passing along company information while sifting it for credentials and other useful data.
Angry customers venting online are vulnerable to angler phishing, in which an apparently sympathetic customer service representative contacts them offering to solve the problem and all that’s needed is their…PII.
Given the focus on email and messaging based phishing, it’s sometimes difficult to sift well-intentioned but unsolicited messages, routine but poorly phrased communications and legitimate notifications from an avalanche of spam liberally laced with harmful emails.
Software tools can flag the most obvious of these phishing attempts, but social engineering is becoming more sophisticated. The public information that individuals share on social media fuels more realistic phishing attempts, which in turn get linked to that personal information to create persuasive digital identities.
That’s the endgame and the only effective response is to limit not just private, but also unnecessary public information sharing to short-circuit the process.
Share what’s necessary. Confirm before giving anyone your PII either on the phone, via email or on a web form. Insist on proof of identity from anyone contacting you and communicate directly with any business they claim to represent.
The ISC2 has published a list of phishing tactics here.








































[…] Caribbean – According to a 2021 CISCO report, most successful data breaches, more than 90 per cent, are the result of data phishing… more […]