- Hackers exploit vulnerabilities in technology, processes, and human behavior.
- Government, manufacturers, vendors, and users must collaborate to address cybersecurity challenges.
- Focus on fundamental security measures like backups, segmentation, antivirus, and firewalls.
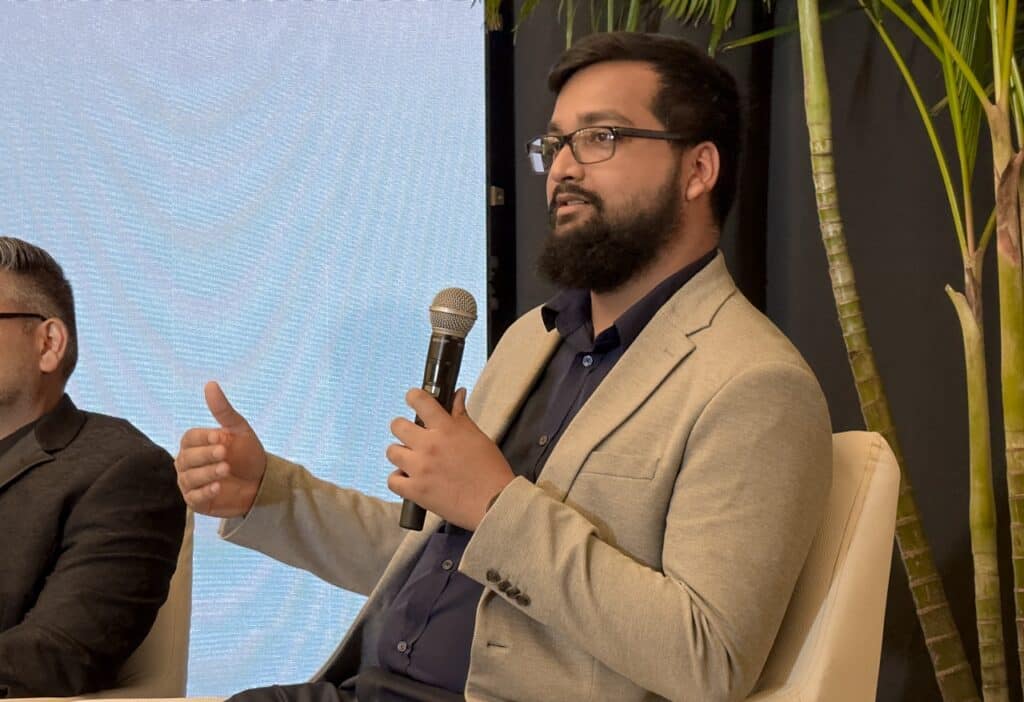
Above: Huawei’s Gabriel Nunez. Photo by Mark Lyndersay.
BitDepth#1488 for December 09, 2024
“We realised, in almost every single [digital breach] incident, the first thing is the hack,” said Anthony Peyson, president of the regional chapter of ISC2 on November 30 at the association’s inaugural Scam Defence 2024 seminar.
“You can hack technology. We know about hacking technology where the hacker breaks into systems. You can hack a process. You don’t often find a spotlight on that. And you can hack a human.”
ISC2 is the merciful acronym for the International Information System Security Certification Consortium, a global collaboration of cybersecurity professionals.
The Caribbean chapter was formed earlier in 2024 in the face of the global surge in cyber threats.
According to Peyson, Latin America and the Caribbean have faced 137 billion cyberattacks in the first half of 2024 alone, a 50 per cent rise over the same period in 2023.
The Scam Defence seminar was the first of a planned annual symposium discussing developments in cybersecurity and the changing face of how access to personally identifiable information (PII) from companies and individuals is being engineered.
The regional chapter has determined that the biggest challenge the Caribbean faces is phishing (fake emails and web links) and smishing (fake SMS text messages), both facets of growing sophistication in social engineering techniques.
“We are here to raise awareness, to educate the public and to foster collaboration, we are community,” Peyson said.
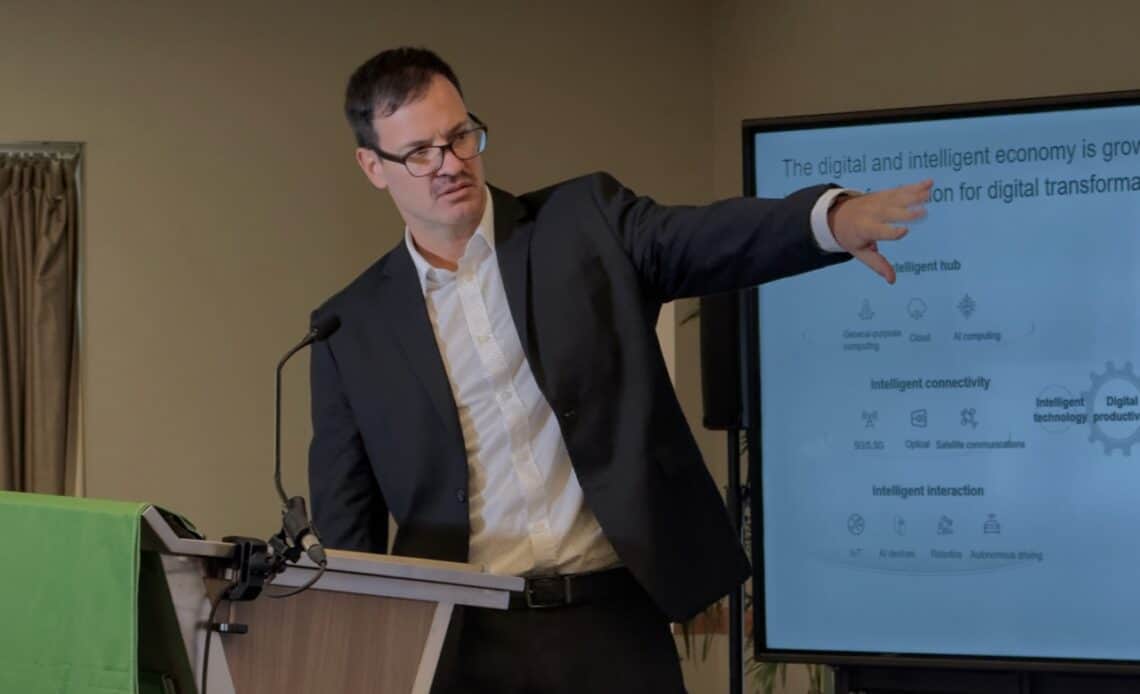
At stake is the vulnerability of growing digital and intelligent economies to hacker takedowns.
Gabriel Nunez, Huawei’s Cybersecurity and Data Protection Officer for Latin America and the Caribbean believes that economy will grow from US$3.6 trillion in 2020 to $18.8 trillion by 2030.
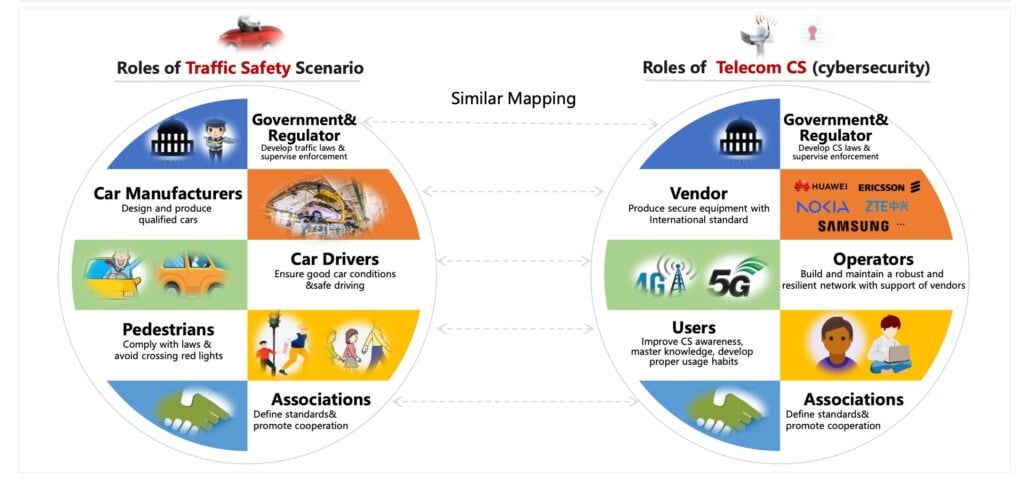
Nunez saw parallels between how traffic is handled successfully through a collaboration of government and regulators, manufacturers, vendors, users and system architectures that might better protect digital systems.
“Government and regulators develop laws and supervise enforcement, manufacturers produce qualified equipment to international standards, vendors are certified and follow the rules and users comply with laws and rules and avoid known dangers,” Nunez said.
“No one can solve the traffic problem. Alone, they will not solve the traffic problem. We all have to interact.”
The world is moving, though far more slowly than the Internet’s bad actors, toward that kind of collaborative thinking.
Digital nation strategies have been released by 170 countries and regions and more than 60 countries have elevated AI in their national strategy. Action plans for green development have been released by 151 countries and regions.
All 193 UN member states can contribute to the draft UN Convention against Cybercrime, which includes legal support to support the criminalisation and prosecution of 11 key cybersecurity crimes across all UN nations.
Meanwhile, Caribbean nations can also consider benchmarking against the Global System for Mobile Communications Association’s (GSMA) Network Equipment Security Assurance Scheme (NESAS), which has been widely adopted and the association’s Mobile Cybersecurity Knowledge Base (MCKB), which has been adopted by 13 countries.
Both voluntary standards align with the telecommunications safety standards proposed by the 3rd Generation Partnership Project (3GPP).
There’s no shortage of acronyms and technicalities available in the backroom of technology, but the real challenge facing cybersecurity experts is balancing the need to explain the dangers that users face – both as individuals and on behalf of the companies they work for – with the diligence they need to safely work with internet-connected computers.
The consequences of failure for the region on this critical frontline are dire.
“When we go in and we do a root cause analysis to figure out exactly what happened, what we realize is that it’s very small things that add up all together and lead to a full compromise,” said Anish Bachu, Manager of the TT Cybersecurity Incident Response Team.
“So when we’re looking at defending ourselves, the emphasis should be on doing the basics well. We [should] have good backups, good [network] segmentation, antivirus and firewalls in place.”
“As soon as we see (a phishing attempt) on social media, our team acts to have the links they lead to taken down. That’s part of our responsibility right there.”
“Phishing that takes you to a particular site, we act to take that site down as soon as we are aware of it. So even if somebody comes after and clicks on the phishing link, it goes nowhere.”
According to Bachu, there were 52 breaches reported to the TTCSIRT in 2023 and 78 so far in 2024. He estimates that unreported breaches will increase those numbers by 20 per cent.
In addition to greater user awareness, there needs to be clearer reporting lines to action teams like TTCSIRT for the public and more active internal reporting of dubious messages and texts within companies.
Next week, the hacks that keep regional cybersecurity professionals awake at night.