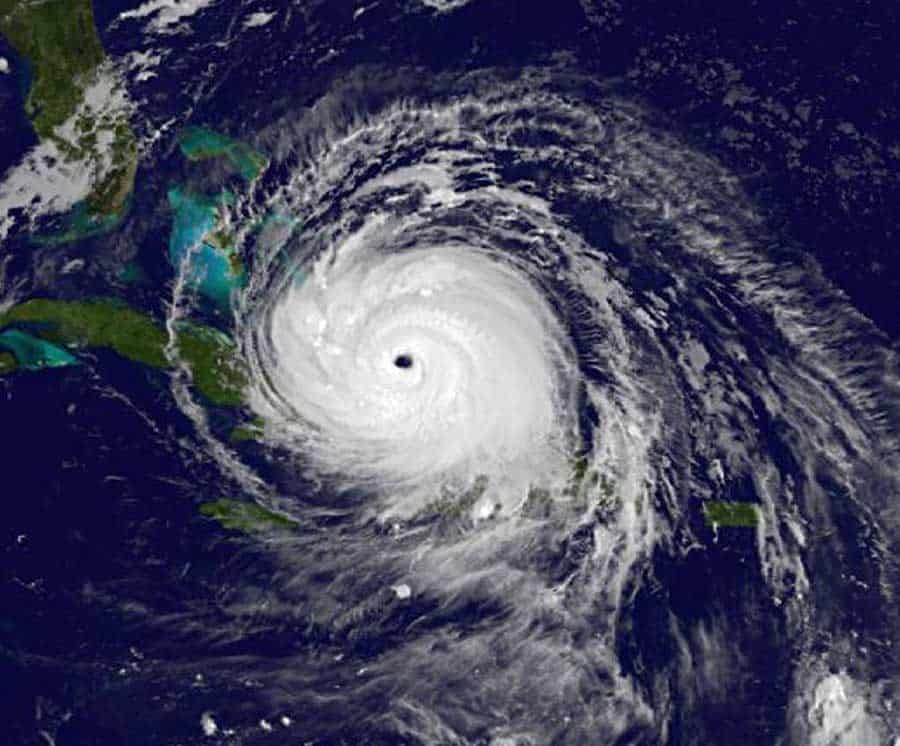
Above: NOAA’s GOES East satellite captured this infrared image of Hurricane Irma in the Bahamas at 4:45 a.m. EDT on September 09, 2017. Image courtesy NASA/NOAA GOES Project
Coded-Arts, a Caroni based digital company specialising in websites and gaming has created an online resource for people wishing to report their status in Caribbean islands hit by hurricane as well as to check on the status of loved ones.
There are currently three named tropical storms active in the Atlantic, Katia, Jose and Irma.
The site is spartan and direct and loads quickly, providing its information quickly on mobile devices in low bandwidth situations. The Android app will go live by 4 pm today and the website is currently active and receiving information.
Despite adding a CAPTCHA system to repel automated attacks, the site has already weathered two attempts at hacking via SQL injections.
According to Browne, “There have been instances of where hackers have attempted to breach the network. Though they have all failed, what surprises me is the strong desire to do so.”
“These attacks have to be people based. The intention here is to help, and already, people are attempting to hinder that.”
According to a release from Coded-Arts…
“The new website combines a comprehensive listing of user information and there last known whereabouts and a directory of missing/ found individuals.,” said Manuel Browne, Managing Director of Coded Arts.
“The site will be of tremendous value for people seeking information in this fashion. This is a straightforward web app that also is provided on the Android app store (it is still review for iOS distribution). We have prepared the web app and mobile app for heavy loads of traffic and for ease of use, and we’ll be extrapolating on it, with the help of developers volunteering to expand it.”
Updated 09-o9-17, 2:30pm with details about the attacks on the website.
“The first DDOS attacks occured around 10-11pm last night,” Manuel Browne said, “which was partially expected traffic due to the amount of posts, sharing, boosting and activity surrounding it.”