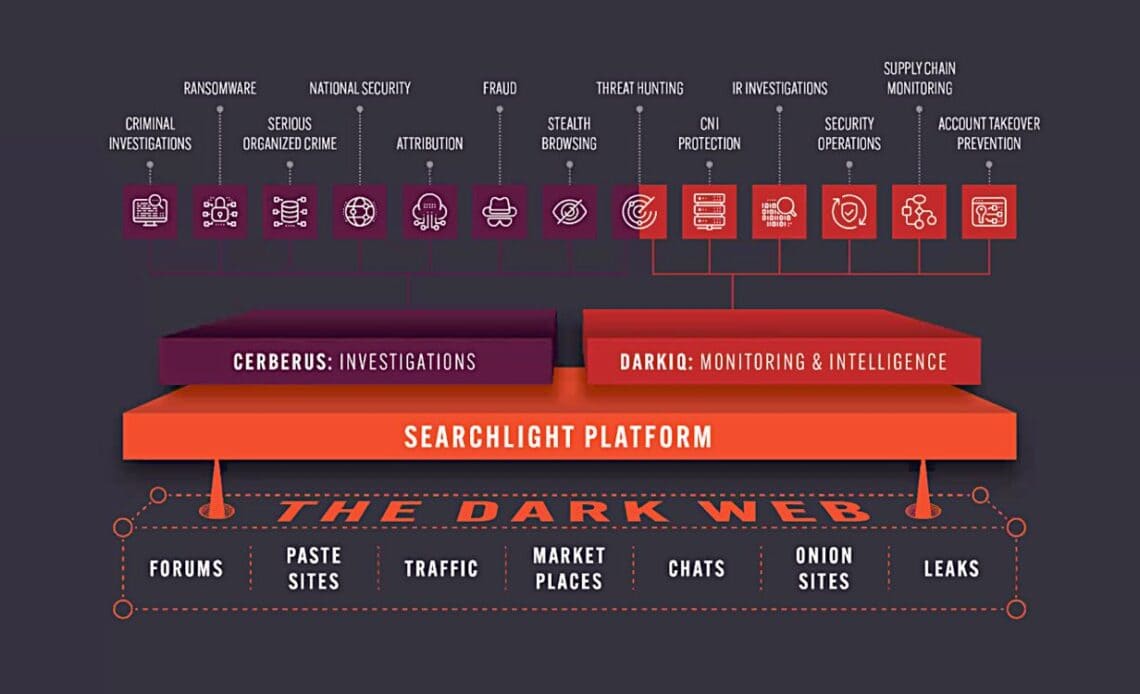
Above: The architecture of Searchlight Cyber’s monitoring system.
BitDepth#1421 for August 28, 2023
Calibra Solutions hosted a webinar on Thursday about the tools it brings to bear on improving cybersecurity, with a particular emphasis on threat intelligence.
Calibra is a 15-year-old regional solutions provider with an impressive client roster of TT businesses and state enterprises led by Managing Director George Whyte.
Based in Trinidad and Tobago Calibra offers its services in the English-speaking Caribbean as well as in the Dutch-speaking islands of Suriname, Aruba, Curacao and Sint Marteen.
The company offers a range of IT consulting and advisory services and delivers business analytics using Qlik analytics and financial application software for banks and corporations through its partner Mimics.
The company’s capacity to monitor and respond to threats on the darkweb is a focus of its business partner Searchlight Cyber.
According to Nick Savage, Head of Infrastructure, Security and Compliance at Searchlight, the company began out of early explorations of Bitcoin and surveys of the digital currency’s use on the darkweb.
The company accesses the anonymous sites on the darkweb using its software platforms, Cerberus, which it uses to investigate activities and DarkIQ, which is tasked with using that intelligence for monitoring and preventive analysis.
To do this, the company accesses the anonymous onion sites of the dark web to extract information about what is being posted or pasted there, extracting and analysing information about data dumps and compromised hardware that’s being sold to host malware.
Searchlight works closely with law enforcement when it finds actionable material, such as leaked information and credentials.
“Cerberus is great for performing investigations on what has happened or investigations on actors that you’re interested in or investigations on [specific] things that you’re interested in,” Savage said.
“You can see what [potential bad actors] are currently doing, see what else they’ve done, and interact with all the intelligence that we’ve gathered about those actors that may help to deanonymise them if you want to go through the process of possibly arresting them.”
“We’ve found the service to also be really useful when it comes to performing investigations about what happened in the past. I’ve had the misfortune of being at an enterprise that had a ransomware attack that closed everything down. On Cerberus, we had an early warning sign about this happening a week before.”
“To take the information that we have available and present it in a more proactive manner, we’ve developed DarkIQ which delivers alerts about the information that gives early warning signs of threat actors operating on the dark web that may be targeting you, that may be targeting the type of equipment that you’re using, vulnerabilities that exist in that equipment or that may be targeting particular exploits that you need to be aware of to bring in additional mitigation or protection.”
The company doesn’t only gather current dark web information, it archives data that normally exists only for a short time on onion sites and has records that go back for at least two decades.
That makes it possible to have investigations into information that no longer exists on the darkweb about drug marketplaces, cryptocurrency transactions and ransomware groups, enabling deeper analysis and correlation of activities and bad actors.
“This open source intelligence helps take you from the nebulous environment of the dark web to identifiers that you can use in the real world,” Savage explained.
“For law enforcement [you might] use a server that will give you the evidence that you need to go through to prosecution.”
“Dark IQ is a proactive monitoring platform that allows you to gather all the data you can with Cerberus, but do it in a proactive way. Instead of going off to look for all this information, it is presented to you as actions.”
“If we’ve identified credentials that are associated with your company, corporate IP addresses that are interacting with sources we deem to be high risk, identified mentions of compromises in your company’s endpoints, or people who are attempting to sell access. We will present that to you as an action that you will be able to respond to.”
According to Savage, the ransomware group Conti made US$170 million in the first year of operation. “These are big enterprises from a national security point of view.”
The Clop ransomware group, which has been exploiting a MOVEit vulnerability has been so successful, Savage says that at one point their webpage had a notice, “Please be patient, we will be with you shortly.”
Nick Savage explains how the dark web works (partially paraphrased from his presentation during the webinar)
The darknet, which runs on the internet backbone, was originally developed as a means of enabling privacy for its users, creating anonymity through theoretical networking constructs.
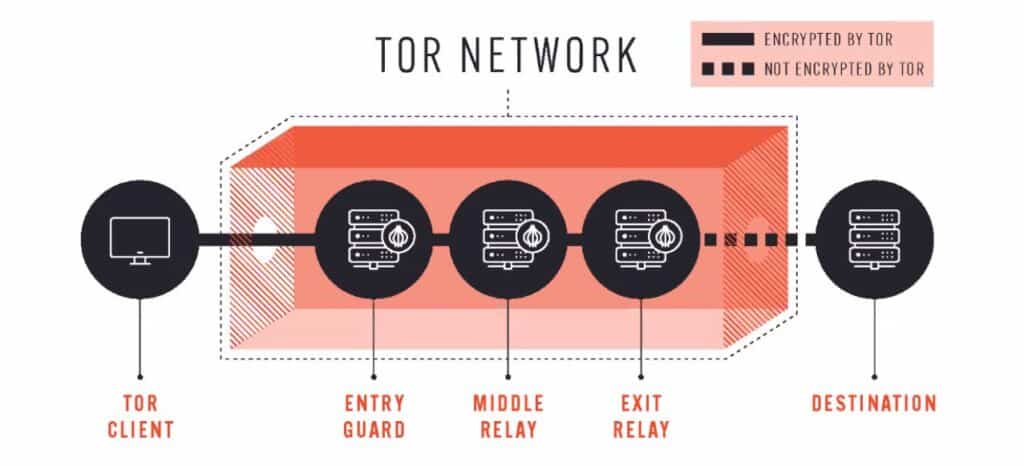
One of those constructs is onion routing, which is what the Tor browser uses to establish anonymity.
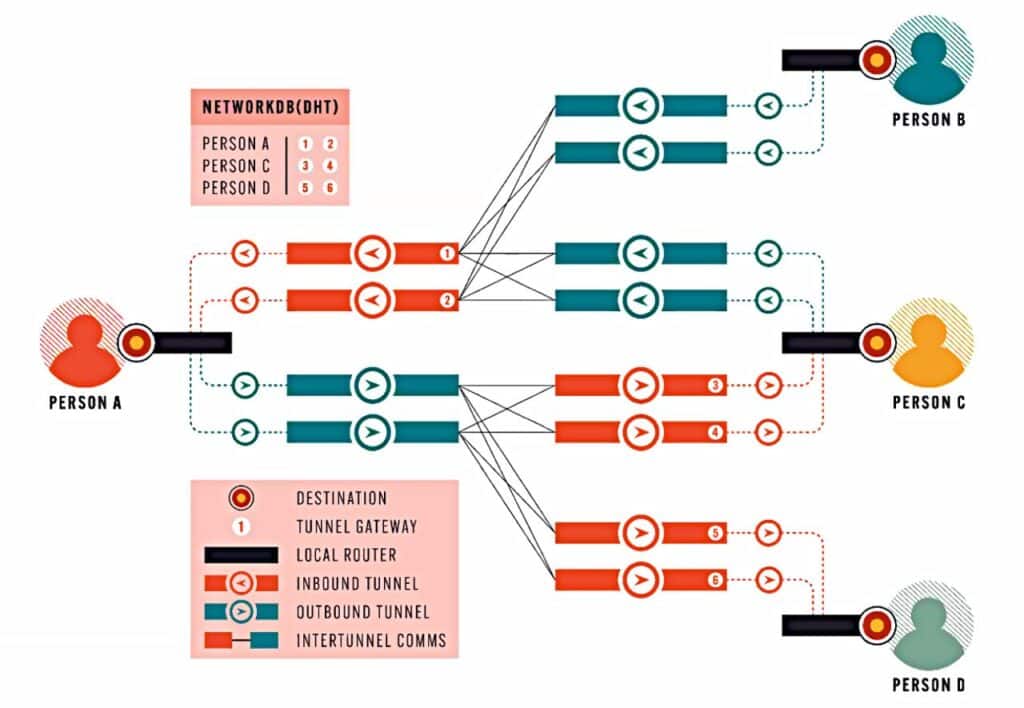
Another construct is garlic routing, which is what Invisible Internet Project (I2P) uses to maintain anonymity, so we have a technical infrastructure that attempts to minimise or effectively eliminate the ability of an end server to know who it is communicating with.
There were also additional things added to Tor, which are called onion sites, websites that exist only within that anonymisation network.
For a v3 onion address for Tor, you would gain access to this with the end identifier of the onion.
You would then contact the directory service. The directory service will enable you to access an introductory point, the introductory point takes you to the viewpoint through which you’d make a connection to the onion server.
Neither the web server nor the end user know the identity or the IP address of the other.
It’s an anonymisation tool. Not only anonymising the user on the internet, but also anonymising the website, anonymising the endpoint, so everybody is kept within the within the darkweb ecosystem.
The onion router network has established the greatest number of nodes, hardware relays through which computing power is contributed.
In order to maintain the Tor network, the total network has around ten thousand of these relays.
The tool builds a network of these servers across the internet using encryption so individual relays don’t know the next step for the subsequent hop after that.
On the I2P, servers are volunteered to be a part of the I2P network.
I2P attempts to combine cells of information from different people, put it into one blob of encrypted information before sending it across the network.
The Tor project claims that its users are whistleblowers, journalists, bloggers, IT professionals, law enforcement, business people, “normal” people.
Famous uses include drug marketplaces (Silk Road, Hansa) and child abuse material.
News agencies create darkweb sites to allow whistleblowers to contribute information to them anonymously. If you’re in a country that has a fair amount of restrictions on network access and where and to whom you are connecting, that is a useful thing to have.
Savage reports that most of the requests to particular sites were to sites that either contained illegal material or were associated with illegal activities.
There are more than 500,000 Tor onion websites on the darkweb.









































[…] Trinidad and Tobago – Calibra Solutions hosted a webinar on Thursday about the tools it brings to bear on improving cybersecurity, with a particular emphasis on threat intelligence… more […]