Above: Illustration by ArtemisDiana/Depositphotos
BitDepth#1415 for July 17, 2023
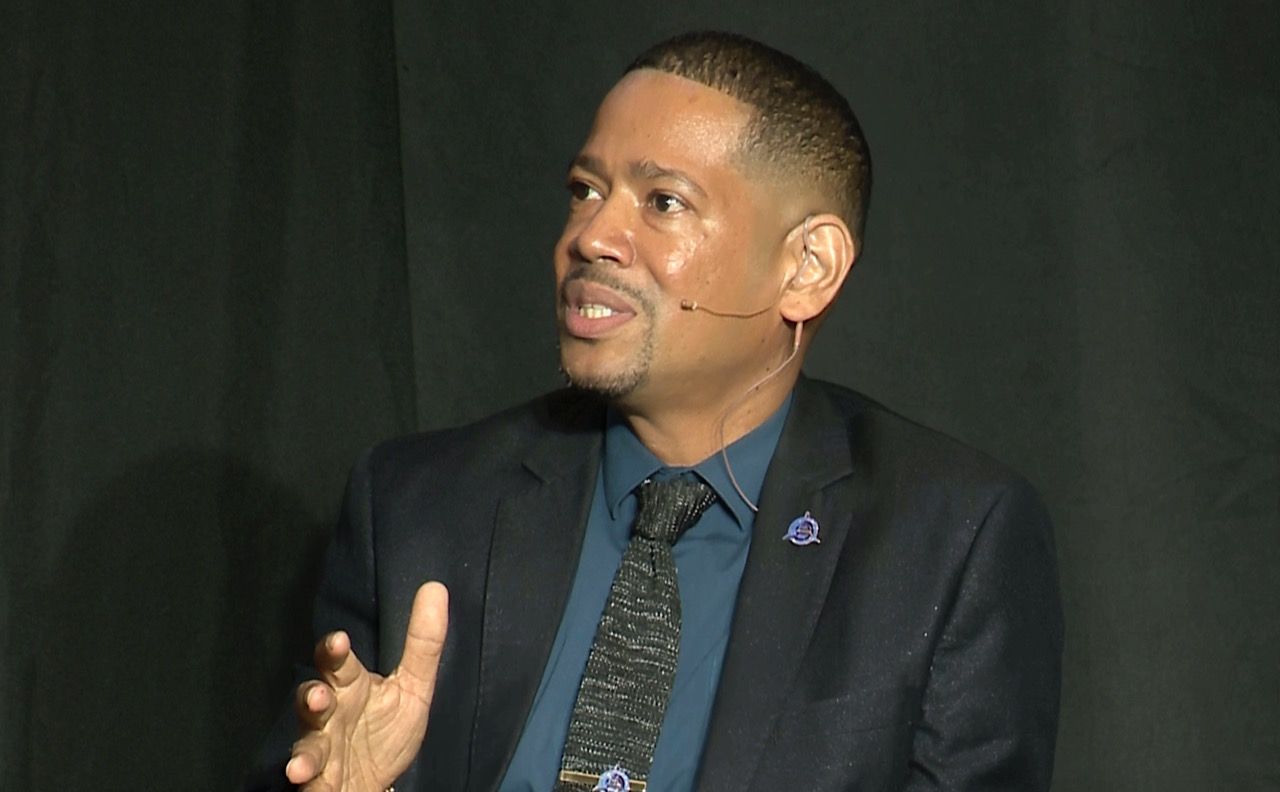
Leading the June 29 panel discussion on building a security minded culture at the AMCHAM Tech Hub Islands Summit, Bryan Kane, Innovation Director for Digicel Business, offered a provocative question.
Putting two links to a Digicel website up on a slide; he asked a room of experts which was the fake.
Kane was demonstrating a homoglyph domain used in phishing, which disguises the real URL by using a letter from another language in the domain name.
The “L” in Digicel was a letter in another language that appeared identical to the Latin character set.
Microsoft analysed 1,700 homoglyph domains between January and July 2022 and discovered that 170 techniques were used to disguise URLs, but seven per cent of domains used just 14 techniques.
Quick tip. Hovering your cursor over a text URL on most modern operating systems will reveal the actual link you will be directed to.
“Seventy per cent of attacks are the result of human error or misunderstanding,” Kane said. “People are the major culprits in cybersecurity lapses.”
“I want you to remember that every single day within your organisations, your people, your citizens, your employees, your users, are having to deal with all these things, all the time. So they’re receiving emails, Teams messages, SMS messages. How do they know what’s real and what’s not?”
The consequences can be dire. Vitra Gopee, moderator for the panel discussion, noted that according to IBM, it takes an average of 197 days to identify a security breach and 69 days to contain it.
Factor in the months that can be lost trying to reconstruct lost business records and the cost of cybersecurity prevention begins to look much less expensive.
“I work with a lot of customers throughout the region and there is there is a gap between the board and CEO and cybersecurity,” said Stephen Juteram, VP for Sales at Hitatchi.
“What we’ve seen happen is that organisations are taking strategic decisions for digital transformation and in many cases, cybersecurity is an afterthought.”
“We’ve started to see more chief information security officers being hired to be that person at the C-Suite level, making sure that security and privacy are embedded by design into the projects from day one.”
“Some businesses can’t justify having a full time CIO, so organisations have been offering those services to give boards support in making those decisions.”
“CEOs are responsible for cybersecurity,” agreed Kane.
“When a board of directors hires a CEO [cybersecurity] needs to be an interview question during that stage. Because when you think about it, CEO’s can be fired for [the consequences of] a cyberattack. Now it’s a boardroom conversation.”
But Kane also advocates a company-wide response to the growing cybersecurity threat.
“To build a cybersecurity minded culture, it’s really all about education. Teach everybody everything. From the CEO, all the way down to every individual user within the organisation. Everybody needs to understand why they’re part of the problem and how they can be part of the solution. Don’t leave any gaps. The CEO or the CIO is responsible for how this happens.”
“People are causing the problem, but people are also the solution to the problem. [It can be] very hard to get them understand that and get into that cybersecurity mindset.”
“When you can’t get the people to guide the organisation, it becomes very difficult to manage things, to decide how to do things, how to implement, what to buy, how to buy it.”
The cybersecurity challenge is only going to grow as artificial intelligence begins to power tools. AI doesn’t need nap-time or breaks or vacations, Kane warned.
“It just keeps going until it finds a way into the organisation, and then it passes that [access] on to a hacker.”
“AI can bring 24 -7 [response] visibility, it brings you to that point where you’re able to collect information, analyse it in real time, you’re able to isolate and you’re able to repair and remediate.”
“[Let’s say that] Brian logs on to his laptop in Trinidad and then 20 minutes later, he logs on to his laptop in Poland. That sort of behaviour is not normal. AI can now detect this and help you to isolate Brian off the network, protect everybody else while we’re dealing with Brian. Brian’s a nuisance.”
Kane warns that spending money on cybersecurity doesn’t improve safety.
“There are companies who spend hundreds of millions on cybersecurity, but they still get breached every single year, so it’s really about how cleverly you implement it, who’s watching in real time, what are you doing every single day of the week?”
“Are we missing some of the alerts that are coming in every single day? Are we catching everything and filtering correctly?”
The most important thing is to make a start and make it a good beginning.
“Stay vigilant.” Kane warned. “Don’t allow them even an inch into your infrastructure. Do not give them any opportunity to get in. “
“Always look for new ways to protect yourselves. Always be training your staff. Be vigilant when they’re following the frameworks that you’ve laid out for them.”
“And it’s simple things. You know the password policy? Nope? If you don’t change a password, you’re off the network. Be diligent about it. Be strict about it.”
“I believe in execution, I believe in beginning, I believe in starting something, even if it is just the basics. Even if it’s just the training and the endpoint protection with just those two things alone, you can reduce your attack surface by up to 85 per cent.”