- Unpatched systems, especially older versions of Windows, are highly vulnerable to exploits.
- No single solution can provide complete protection; multiple layers of defense are necessary.
- Companies are using unsecured channels like WhatsApp, exposing themselves to potential security breaches.
Above: AI Illustration from 123RF.com
BitDepth#1489 for 16 December
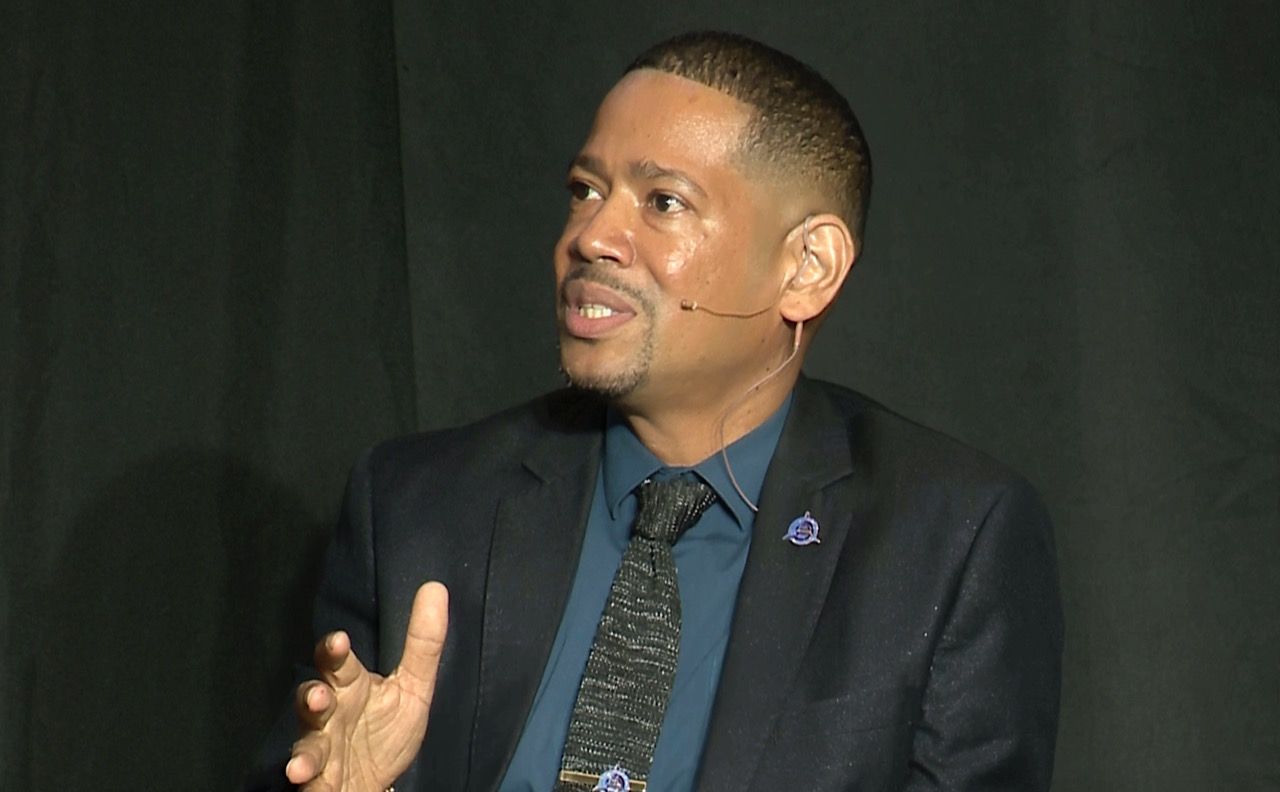
The panel discussion that comprised the second half of the ISC2 Scam Defence seminar on November 30 made clear some of the challenges that regional cybersecurity experts face.
Those hurdles include a reluctance to retire aging, vulnerable equipment, fundamental misunderstandings by C-Suite management about areas of digital weakness and poorly implemented network security regimes.
Dark web researcher and penetration tester Shiva Parasram explained the history of the EternalBlue exploit, created by the National Security Agency of the US government.
The NSA engineered the exploit in 2012 to access computers running then current versions of Microsoft Windows but didn’t tell the company anything about it until 2017, when the Shadow Brokers, a hacker group, got hold of the code and released it widely.
Microsoft quickly engineered and released a patch, but unpatched systems remained vulnerable and the WannaCry virus used the exploit to spread, causing millions in damage and downtime.
If the vulnerability remains unpatched on a modern system, the likelihood of a successful breach is close to 100 percent.
Microsoft took the unfortunate step of first releasing the patch to users running then current versions of Windows and customers on the company’s thousand dollar extended service contract.
The patch was eventually released widely and for free for systems running Windows XP and up.
“It’s a bit worrying because there are a lot of systems that still run [older] applications and you can’t upgrade them,” said Parasram.
“If I were to jump on a Kali Linux system and I found one of those older systems on Windows 7 or Server 2000 it would take two to five minutes to fully compromise the system. There are hundreds of thousands of exploits out there and it’s pretty tough to defend against them all.”
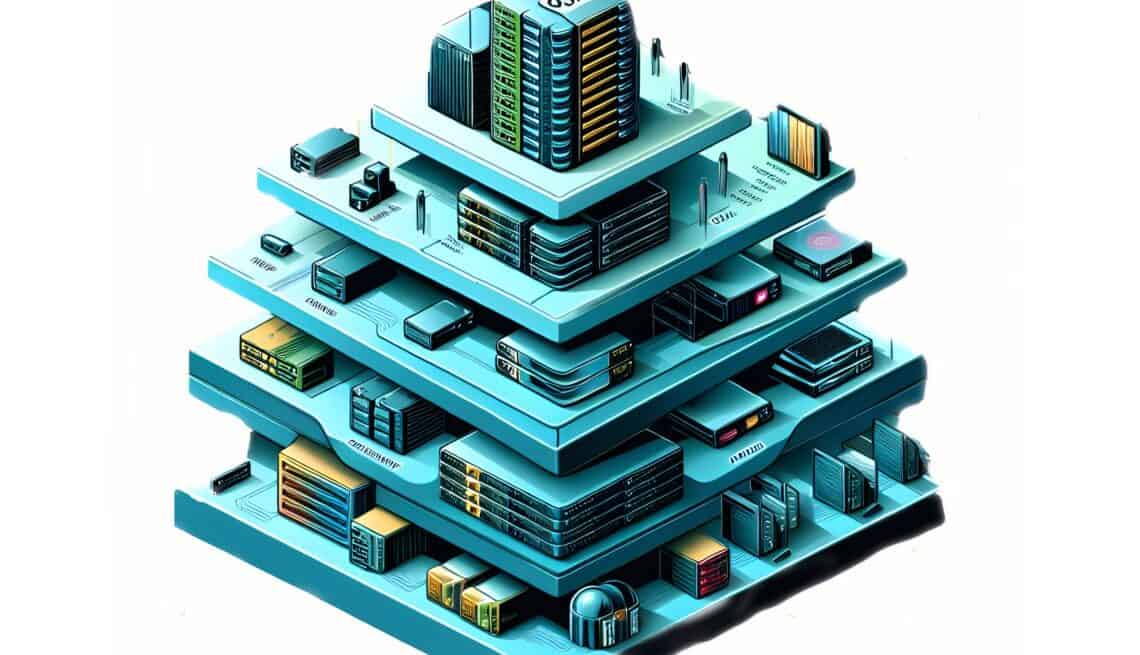
“In a network, there are lot of vulnerabilities and they can happen at different levels of your technology,” said Ajmal Nazim, cybersecurity consultant and systems auditor.
“If you look at the the traditional OSI (Open Systems Interconnection) stack, you have seven layers from physical all the way up to the web applications, and each one of these stacks is going to be susceptible to vulnerabilities.”
“You have to have a holistic approach. There’s no single solution that will give you overall protection.”
“You have multiple layers. And should one of them fail, then you’re hoping the others will stop the hacker from getting in.”
Whether the attack comes from a successful external attempt, exploiting a vulnerability or from inside, perhaps a disgruntled employee, an exploit needs just one vulnerability.
The attack can then move laterally throughout the network and through an escalation of privileges, can compromise the entire network. They will encrypt your entire network, they will exfiltrate data. They will demand a ransom.
“Companies will think that once they have a firewall in, then they have done what’s needed,” Nazim said.
“The firewall is your perimeter, it’s your first line of defense. But once you get inside of the network. then you need defenses and a proper segmentation of the network.”
“So if they do breach the perimeter, then it shouldn’t be that it’s a free for all on your internal network, no matter how big it is. The infrastructure should be properly segmented so if anything they’ll only get into one segment.”
Scofield Thomas, Managing Director of 800-TECH offered examples of worrying real world experiences.
In one instance, he found a client running the business without a firewall. “It was giving trouble, it was blocking things, so we took it out,” was the response.
“I recently spoke with a new client who is running Microsoft Server 2003,” Thomas said.
“It’s a critical industry that they’re in and this server is vulnerable. The issue is about two things, supporting this core, legacy application that they feel the need to hold on to that they can’t upgrade. Then there is the cost.”
“You have this critical information on a server that is unpatched. These are the small mistakes that you make. You think you’re being budget conscious, but in the end the reputational damage and expense can be immense.”
“I’m trying to understand why a lot of companies don’t utilize encrypted emails or an encrypted e-mail service because the type of information that they send over insecure channels is crazy and they are exposing themselves to a man-in-the-middle attack.”
“These are the kind of things that we see happening more consistently. I’ll have a client who wants to pay for a subscription service, I’ll say hey, I’ll help you out next time.Then you send me all your credit card information via WhatsApp.”
“These are the practices that we have to stop. We need to understand that these channels are not secure.”
“At one company that we represent, one of the C-Suite people who approves financial transactions comes to me and says I have these seven missed calls back-to-back. I keep saying hello, hello, hello. Is anybody there? I called my cybersecurity engineer and he explained that it’s a deep fake. They’re trying to capture his voice and run it through AI to use it make a call [masquerading as] him for approvals.”
Parasram noted the increased presence of information stealers like Lumma, which target cryptocurrency wallets and two-factor authentication browser extensions to steal sensitive personal information from a victim’s machine.

“Ever notice that every single time you try to log back in, you’re not asked to provide [authentication credentials]? It’s stored in a session, and information stealers capture your username, your password, they steal the actual session that you’re working on.”
“That information is sold to other companies and there are hundreds of forums on the dark web. Sometimes it’s sold, sometimes it’s given. There was a Telegram group for the Redline information stealer. That was taken down recently. They were selling access for US$100 per month.”
“There were around 32 big leaks in the Caribbean for 2023. Terabytes of information are definitely out there. That includes things like your bio data scans for your passport, utility bills, letters requesting services.”
“The thing that keeps us awake is just the potential of the threat actor to just blend in with the regular traffic on the network, said Keisha Langley, cybersecurity specialist, CBTT.
“In our ongoing monitoring, things that fall outside of what is normal for our operations are key things we have to keep our eye on because we know that they can really just blend in very easily. The good guys (white hat penetration testers) show us so that we can get better.”
“But I just think it’s important for us just to look at a number of different things and different potential indicators when we’re monitoring our environments.”