
Above: Irene Yeo and Nelson Chia present Flexxon’s cybersecurity solutions at the Mariott. Photo by Mark Lyndersay.
BitDepth#1459 for May 20, 2024
On Tuesday, Pinaka Consulting hosted an enterprise-level introduction to Flexxon’s® X-PHY® cybersecurity products.
Pinaka has previously been involved in blockchain and central bank digital currencies consulting along with ransomware tracking on the blockchain before taking this new step into hardware protection solutions.
Pinaka CEO Shiva Bissessar called on local businesses to begin taking the role of Chief Information Security Officer (CISO) more seriously, and to consider integrating the position into upper-level executive level decision-making. The company will represent Flexxon® locally and in the Caribbean region.
“Pinaka has traditionally focused on information security based consultancy,” said Bissessar.
“In stepping into the cybersecurity solution provider role, we sought to bring unique innovation to the local and wider regional Caribbean market.”
Flexxon was represented by Irene Yeo, who gave an explanatory keynote on behalf of the female founded and led Singapore cybersecurity company.
Flexxon began business in 2007 under the leadership of CEO Camellia Chan with a line of products that targeted niche industrial, medical, automotive and aerospace sectors before making a change in 2017 to static security solutions.
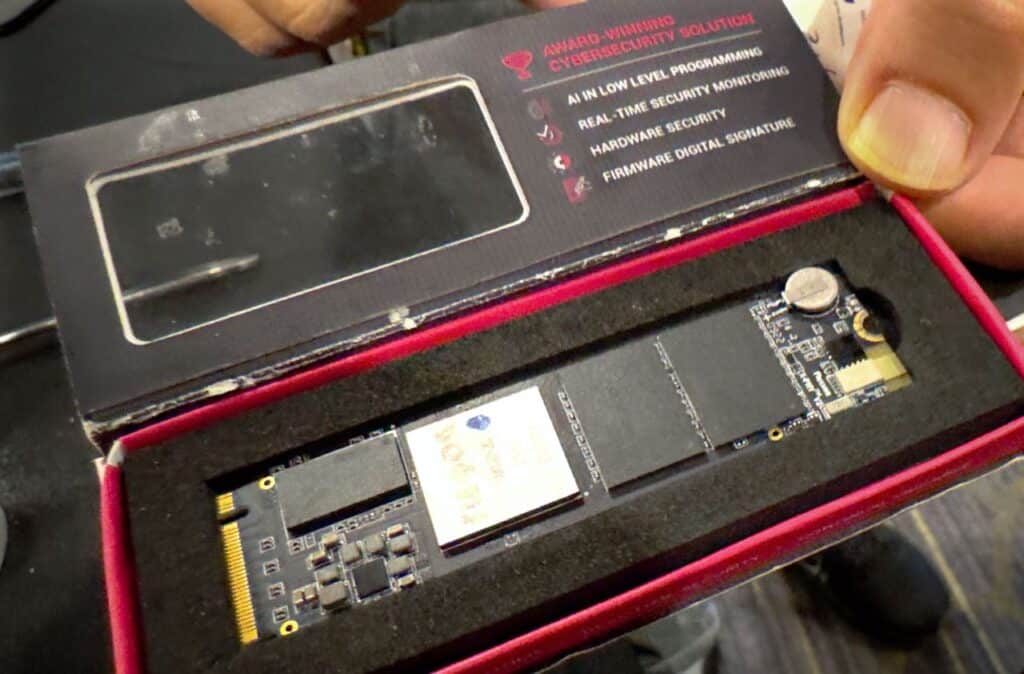
By 2019, those solutions had evolved into the company’s first X-Phy secure solid state drive (SSD) with embedded artificial intelligence.
Flexon introduced its newest hardware protection systems last week, a NAND flash memory solution that’s available in an NVME form factor as well as a one-slot PCI-E card for enterprise installations.
The new X-PHY product provides hardware level security that doesn’t conflict with other software solutions save for drive level encryption products, since the cyber secure drive does its own encryption as part of its protection regime.
The SSD-based hardware protection delivers a broad range of security responses by first creating a single access point through which data flows.
The resulting data stream is monitored by software that’s embedded in a chip that’s part of the drive hardware itself, providing a continuous review of access patterns using AI in the chip controller that monitors for possible malware intrusions with real-time detection and response to suspicious activity or patterns of attack consistent with known malware.
The on-chip AI intelligence can lock out new threats by isolating unusual patterns of access.
Regarding updates to the software embedded in the X-PHY, Flexxon responded via messaging that, “We do not need constant updates like software [solutions].
Our [infrequent] updates are for firmware or feature updates only. Detection is based on read/write/overwrite [patterns] within the drive and all commands need to bypass the firmware on our chipset for analysis and detection through the one door access [implemented using] the PCIE and NVME protocols.”
Yeo noted that an increasingly critical vector for data breaches and leaks is lost or stolen devices. Flexon’s drive level security measures for SSDs and other flash media storage devices offer a defence against intrusions even when hardware is no longer under the control of a company or its agents.
Flexxon has established partnerships with Lenovo, Asus, Dynabook and HP to deliver what they describe as “AI-Augmented laptops” that implement the X-PHY security solutions in a ready-made package. Flexon made no announcements about the availability of this laptop series on the local market.
By 2025, the company plans to expand into enterprise level server and data center installations with Enterprise Server Defender, which will introduce its own stand-alone operating system and applications to the cybersecurity mix, building on drive level protections with live, AI powered detection of data stream anomalies and protection across all seven layers of operating system interconnection.
Server Defender promises multi-level protections on chip, including its patented Matrix Shield technology, proactive live anomaly detection, real-time incident, response, uninterrupted instant restoration and unidirectional assessment.
According to Flexxon’s promotional materials, “Server Defender lies outside the process integration stack but tracks all hardware computations happening between the CPU, Platform Controller Hub (PCH), host processor chipsets and the motherboard itself.”
“We constructed a barrier isolation wrapper that monitors operations between Direct Memory Access (DMA) and the host processors, eliminating any extraneous operations in the cache and thereby nullifying the potential for DMA attacks.”
“The reception from the market so far has recognised the unique nature of these solutions in examining the execution of read, write and overwrite instructions at the SSD level,” Bissessar said after the morning’s presentations to local IT professionals.
Both X-PHY products are immediately available from Pinaka Consulting. The Server Defender product is available but is currently in beta.







































[…] Trinidad and Tobago – On Tuesday, Pinaka Consulting hosted an enterprise-level introduction to Flexxon’s® X-PHY® cybersecurity products… more […]