Above: Illustration by swevil/123RF.com
BitDepth#1448 for March 04, 2024
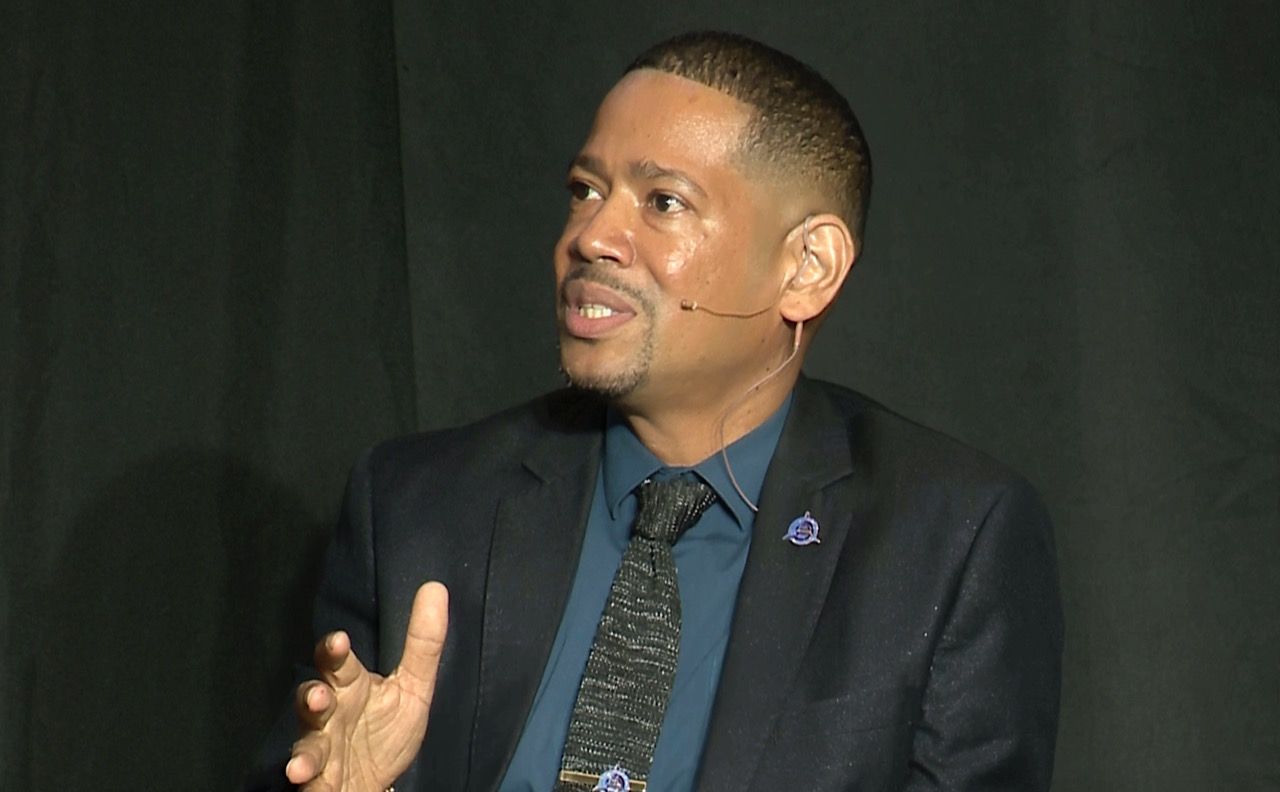
The Ransomware Roundhouse, a report on the state of ransomware in 2023 was launched last week with a webinar discussing the findings and their implications.
The authors, Alex Samm of Tier 10 Technology and Shiva Parasram of the Computer Forensics and Security Institute, acknowledge that their findings are incomplete, based as they are on announcements by ransomware collectives of successful exfiltrations of company data from businesses.
The report lists 32 known breaches among Caricom nations. TT is second in a tie with the Dominican Republic with four known breaches and behind Dominica and Puerto Rico who led with six known breaches each.
The Caricom nations confirmed to have been hit by successful ransomware breaches were Antigua and Barbuda, The Bahamas, Barbados, Belize, Dominica, Grenada, Guyana, Haiti, Jamaica and Trinidad and Tobago.
Among the affected entities are insurance companies, logistics and supply businesses, retail and medical companies and a higher education institution.
The report redacts specific details about the companies or institutions affected, but lists the ransomware collectives responsible for the 2023 attacks.
The 8Base, Lockbit3, RansomEXX, Royal and Hive ransomware groups targeted TT and only Royal is currently listed as inactive.
These are all international criminal businesses, the authors warn, who do not discriminate based on company size, business sector or location.
“In 2023 we learned that no one was safe in the Caribbean region,” Parasram and Samm write.
“The sector, size of the organisation, technologies implemented, impact on the global stage, geo-political affiliations or even the GDP were of no matter. Threat actors were interested only in profits and chose their targets based on who was likely to suffer great losses (or fines where applicable), should they refuse to pay them.”
The authors also expressed concern that the list of 32 regional breaches is probably inaccurate, since it does not list ransomware attacks that ended in payment of the routinely exorbitant demands.
Groups such as LockBit3 list over 1,000 victims on their official dark web leak site for 2023, indicating that ransomware groups have become far more aggressive than seen in previous years and companies and organisations alike are in fact paying the ransoms.”
That conjecture is supported by the increase in ransoms paid in 2023, usually in some form of cryptocurrency.
“According to researchers at Chainalysis.com, the amount paid in ransoms for 2023 amounted to a staggering US$1.1 billion. This figure is almost double the amount paid in 2022 which totalled US$560 million.”
It’s notable that the breaches reported in Trinidad and Tobago were largely found on the dark web after ransoms were not paid and stolen data was released to the public.
The local fuzziness around ransomware is only made worse by the national disinclination to be open about these incidents.
In January, Minister of National Security Fitzgerald Hinds told a workshop hosted by his ministry, Caricom IMPACS and the EU that between 2019 and 2023, the TT Cyber Security Incident Response Team had recorded 205 successful cyberattacks with 52 of them occurring in 2023 alone.
There was no clarity about what the TTCSIRT logged as a successful cyberattack.
Were these attacks that were successful at penetrating a company’s digital security measures?
Were they cybersecurity attacks resulting in the infection of a secured computer system? Attacks that resulted in a data breach of sensitive data?
Attacks that breached secured systems, infiltrated them and suffered exfiltrated data and subsequent ransomware demands?
I ask this, because TechNewsTT, like many websites, is under almost continuous daily probing by dictionary password attacks, code injection intrusions and DDOS attempts.
Once a week, I need to specifically block an IP address for sustained and unrelenting efforts (200 or more attempts in less than an hour) to breach the website’s security systems.
Every attack is unnerving, but there is a steadily escalating scale of severity that this country is not capable – even in the face of widespread public concern – of assessing and tabulating in any meaningful way.
The TTCSIRT generally does not respond to requests for information from this columnist and when a response is given, its brevity approaches haiku.
It’s possible that the TTCSIRT is only reflecting what it is given, which is precious little from companies affected by cyberattacks.
Ransomware groups are unconstrained by geography, bureaucracy and certainly not by pride. They are also largely unconcerned about law enforcement.
Within days of a collective effort by international law enforcement agencies to shut down the darkweb presence of LockBit3, the ransomware group was back at a new onionsite link and posting fresh data, including a dump it alleged was exfiltrated from the FBI.
Local victims have overwhelmingly chosen to be respond to these incidents with a digital omerta until confronted with undeniable evidence of the breaches.
That’s a nonstop ride to where we are now. Nowhere.






































[…] Caribbean – The Ransomware Roundhouse, a report on the state of ransomware in 2023 was launched last week with a webinar discussing the findings and their implications… more […]